tsarpaul / Gloryhook
The first Linux hooking framework to allow merging two binary files into one!
Stars: ✭ 83
Programming Languages
python
139335 projects - #7 most used programming language
Projects that are alternatives of or similar to Gloryhook
Hooking Template With Mod Menu
A small template for Android Hooking with Substrate. (Includes a mod menu written in Java)
Stars: ✭ 59 (-28.92%)
Mutual labels: hooking, elf
Dll hook Rs
Rust code to show how hooking in rust with a dll works.
Stars: ✭ 57 (-31.33%)
Mutual labels: hooking
Injdrv
proof-of-concept Windows Driver for injecting DLL into user-mode processes using APC
Stars: ✭ 541 (+551.81%)
Mutual labels: hooking
Free checker
Simple memory leak finder (for C program) using LD_PRELOAD.
Stars: ✭ 5 (-93.98%)
Mutual labels: hooking
Goblin
An impish, cross-platform binary parsing crate, written in Rust
Stars: ✭ 591 (+612.05%)
Mutual labels: elf
Speedhack
Speedhack coded in C++, inspired by Cheat Engine's own speedhack.
Stars: ✭ 29 (-65.06%)
Mutual labels: hooking
Libobjectfile
LibObjectFile is a .NET library to read, manipulate and write linker and executable object files (e.g ELF, DWARF, ar...)
Stars: ✭ 63 (-24.1%)
Mutual labels: elf
Pcsgolh
PCSGOLH - Pointless Counter-Strike: Global Offensive Lua Hooks. A open-source Lua API for CS:GO hacking written in modern C++
Stars: ✭ 56 (-32.53%)
Mutual labels: hooking
Dithumb
Minimal ARM/Thumb linear sweep disassembler similar to objdump
Stars: ✭ 5 (-93.98%)
Mutual labels: elf
Open C Book
开源书籍:《C语言编程透视》,配套视频课程《360° 剖析 Linux ELF》已上线,视频讲解更为系统和深入,欢迎订阅:https://www.cctalk.com/m/group/88089283
Stars: ✭ 715 (+761.45%)
Mutual labels: elf
Dexcalibur
[Official] Android reverse engineering tool focused on dynamic instrumentation automation. Powered by Frida. It disassembles dex, analyzes it statically, generates hooks, discovers reflected methods, stores intercepted data and does new things from it. Its aim is to be an all-in-one Android reverse engineering platform.
Stars: ✭ 512 (+516.87%)
Mutual labels: hooking
Urmem
[x86] Simple C++11 header-only cross-platform memhack library (hooks, patches, pointers, sig scan)
Stars: ✭ 76 (-8.43%)
Mutual labels: hooking
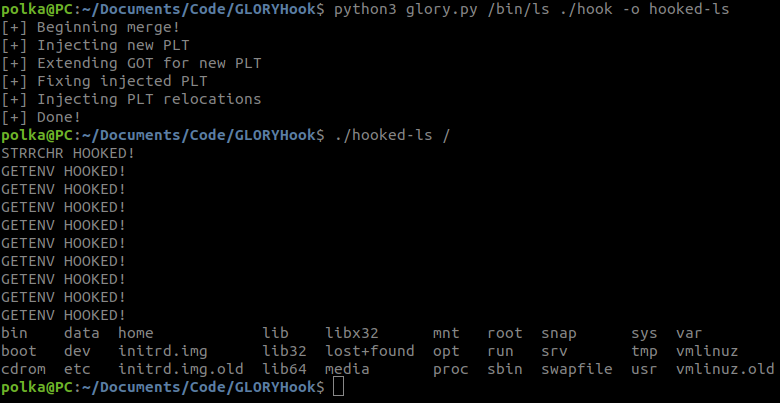
GLORYHook
The first Linux hooking framework to allow merging two binary files into one!
How is this different?
Other hooking methods do not allow calling libraries from within the hook, so you must resort to writing shellcode or your own implementation for libc APIs. This is not the case with GLORYHook. Check out hook.c, you can call any libc API you want!
Use cases
- Debugging - Can't use LD_PRELOAD? Don't want to mess with injecting dependency shared objects and can't bother installing dependency libraries on the system each time? Just hook your file instantly and ship it with zero extra steps.
- File Infection/Backdoor - Can be used as an alternative for an LD_PRELOAD rootkit but with extra stealth sauce. Defenders contact me for how to detect.
Important Notes
GLORYHook supports only x64. Currently hooking is only supported on imports (e.g. libc functions). Currently interacting with globals in your hook is unsupported but will be added soon.
Installation
- Install my custom LIEF (I customized LIEF to make ELF manipulations easier):
git clone https://github.com/tsarpaul/LIEF
cd LIEF
python3 ./setup.py install
pip3 install -r requirements.txt
Usage
- Define gloryhook_<import_to_hook> in your hook file
gcc -shared -zrelro -znow hook.c -o hookpython3 glory.py ./file-to-hook ./hook -o ./hooked-file
Check hook.c and example.sh.
GLORY TO YOU!
Note that the project description data, including the texts, logos, images, and/or trademarks,
for each open source project belongs to its rightful owner.
If you wish to add or remove any projects, please contact us at [email protected].