patois / Hexraystoolbox
Hexrays Toolbox - Find code patterns within the Hexrays AST
Stars: ✭ 202
Programming Languages
python
139335 projects - #7 most used programming language
Projects that are alternatives of or similar to Hexraystoolbox
Hrdevhelper
Context-sensitive HexRays decompiler plugin that visualizes the ctree of decompiled functions.
Stars: ✭ 193 (-4.46%)
Mutual labels: ast, decompiler, ida-pro, idapython
Lighthouse
A Code Coverage Explorer for Reverse Engineers
Stars: ✭ 1,348 (+567.33%)
Mutual labels: ida-pro, idapython, reverse-engineering
Stingray
IDAPython plugin for finding function strings recursively
Stars: ✭ 110 (-45.54%)
Mutual labels: ida-pro, idapython, reverse-engineering
Amie
A Minimalist Instruction Extender for the ARM architecture and IDA Pro
Stars: ✭ 136 (-32.67%)
Mutual labels: ida-pro, idapython, reverse-engineering
Flare Ida
IDA Pro utilities from FLARE team
Stars: ✭ 1,374 (+580.2%)
Mutual labels: ida-pro, idapython, reverse-engineering
Hexrays scripts
Various scripts for the Hexrays decompiler (kloppy, shuffle, arachno, IDA coffee, screenrecorder, ricky)
Stars: ✭ 50 (-75.25%)
Mutual labels: decompiler, ida-pro, idapython
Ida For Delphi
IDA Python Script to Get All function names from Event Constructor (VCL)
Stars: ✭ 92 (-54.46%)
Mutual labels: ida-pro, idapython, reverse-engineering
xray
Hexrays decompiler plugin that colorizes and filters the decompiler's output based on regular expressions
Stars: ✭ 97 (-51.98%)
Mutual labels: decompiler, ida-pro, idapython
Idarling
Collaborative Reverse Engineering plugin for IDA Pro & Hex-Rays
Stars: ✭ 588 (+191.09%)
Mutual labels: ida-pro, idapython, reverse-engineering
Sark
IDAPython Made Easy
Stars: ✭ 477 (+136.14%)
Mutual labels: ida-pro, idapython, reverse-engineering
Lucid
An Interactive Hex-Rays Microcode Explorer
Stars: ✭ 188 (-6.93%)
Mutual labels: decompiler, ida-pro, reverse-engineering
Mazewalker
Toolkit for enriching and speeding up static malware analysis
Stars: ✭ 132 (-34.65%)
Mutual labels: ida-pro, idapython, reverse-engineering
Mrspicky
MrsPicky - An IDAPython decompiler script that helps auditing calls to the memcpy() and memmove() functions.
Stars: ✭ 86 (-57.43%)
Mutual labels: decompiler, ida-pro, idapython
Jremapper
Remapping tool for compiled java programs.
Stars: ✭ 97 (-51.98%)
Mutual labels: decompiler, reverse-engineering
Despector
Java / Kotlin Decompiler and AST Library
Stars: ✭ 126 (-37.62%)
Mutual labels: decompiler, reverse-engineering
Botw Re Notes
Reverse engineering notes and tools for The Legend of Zelda: Breath of the Wild
Stars: ✭ 78 (-61.39%)
Mutual labels: ida-pro, reverse-engineering
Idapyhelper
IDAPyHelper is a script for the Interactive Disassembler that helps writing IDAPython scripts and plugins.
Stars: ✭ 128 (-36.63%)
Mutual labels: ida-pro, idapython
Rematch
REmatch, a complete binary diffing framework that is free and strives to be open source and community driven.
Stars: ✭ 141 (-30.2%)
Mutual labels: ida-pro, reverse-engineering
Abyss
abyss - IDAPython Plugin for Postprocessing of Hexrays Decompiler Output
Stars: ✭ 161 (-20.3%)
Mutual labels: decompiler, idapython
Hexrays Toolbox
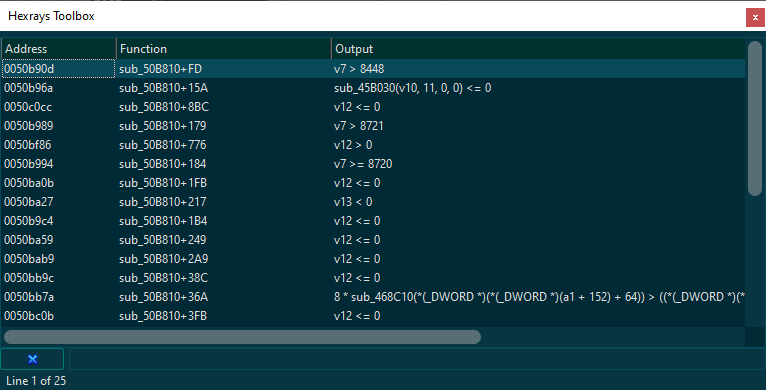
Hexrays Toolbox is a script for the Hexrays Decompiler which can be used to find code patterns within decompiled code:
- scan binary files for known and unknown vulnerabilities
- locate code patterns from previously reverse engineered executables within newly decompiled code
- malware variant analysis
- find code similarities across several binaries
- find code patterns from one architecture within executable code of another architecture
- many more, limited (almost) only by the queries you'll come up with ;)
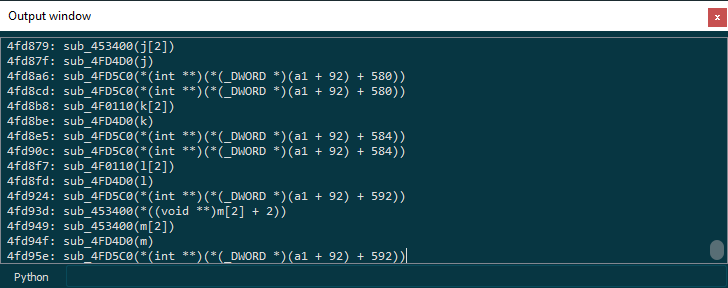
The query shown below can be used to detect CVE-2019-3568 in libwhatsapp.so.
Find the example script
Loading hr_toolbox.py with IDA (alt-f7) will make available the "find_expr()" and "find_item()" functions to the IDAPython CLI and the script interpreter (shift-f2).
find_item(ea, q)
find_expr(ea, q)
Positional arguments:
ea: address of a valid function within
the current database
q: lambda function
custom lambda function with the following arguments:
1. cfunc: cfunc_t
2. i/e: cinsn_t/cexpr_t
Returns:
list of tb_result_t objects
Example:
find_expr(here(), lambda cf, e: e.op is cot_call)
-> finds and returns all function calls within a current function.
The returned data is a list of tb_result_t objects (see hr_toolbox.py).
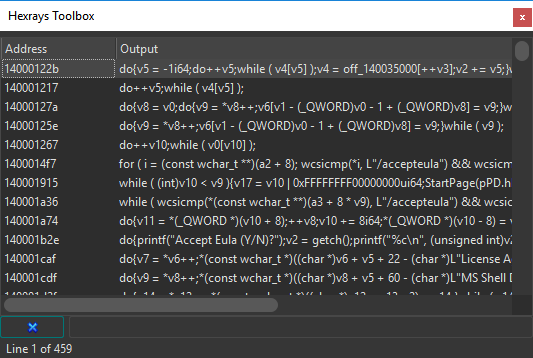
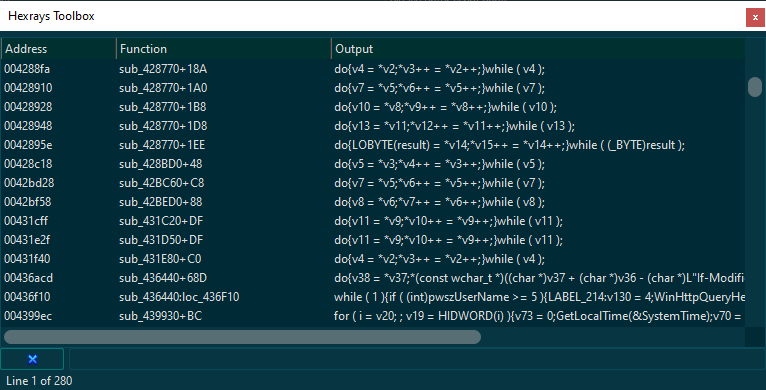
The returned list can be passed to an instance of the ic_t class,
which causes the data to be displayed by a chooser as follows:
from idaapi import *
import hr_toolbox as tb
tb.ic_t(find_expr(here(), lambda cf,e:e.op is cot_call))
Please find the cfunc_t, citem_t, cinsn_t and cexpr_t structures
within hexrays.hpp for further help and details.
Please also check out the HRDevHelper plugin and the IDAPyHelper script which may assist in writing respective queries.
Examples:
- get list of expressions that compare anything to zero ("x == 0")
cot_eq
/ \
x / \ y
(anything) cot_num --- n.numval() == 0
from idaapi import *
from hr_toolbox import find_expr
query = lambda cfunc, e: e.op is cot_eq and e.y.op is cot_num and e.y.numval() == 0
r = [e for e in find_expr(here(), query)]
for e in r:
print(e)
- get list of function calls
cot_call
/
x /
cot_obj
from idaapi import *
from hr_toolbox import find_expr
query = lambda cfunc, e: e.op is cot_call and e.x.op is cot_obj
r = [e for e in find_expr(here(), query)]
for e in r:
print(e)
- print list of memcpy calls where "dst" argument is on stack
cot_call --- arg1 is cot_var
/ arg1 is on stack
x /
cot_obj --- name(obj_ea) == 'memcpy'
from idaapi import *
from hr_toolbox import find_expr
r = []
query = lambda cfunc, e: (e.op is cot_call and
e.x.op is cot_obj and
get_name(e.x.obj_ea) == 'memcpy' and
len(e.a) == 3 and
e.a[0].op is cot_var and
cfunc.lvars[e.a[0].v.idx].is_stk_var())
for ea in Functions():
r += [e for e in find_expr(ea, query)]
for e in r:
print(e)
- get list of calls to sprintf(str, fmt, ...) where fmt contains "%s"
cot_call --- arg2 ('fmt') contains '%s'
/
x /
cot_obj --- name(obj_ea) == 'sprintf'
from idaapi import *
from hr_toolbox import find_expr
r = []
query = lambda cfunc, e: (e.op is cot_call and
e.x.op is cot_obj and
get_name(e.x.obj_ea) == 'sprintf' and
len(e.a) >= 2 and
e.a[1].op is cot_obj and
is_strlit(get_flags(e.a[1].obj_ea)) and
b'%s' in get_strlit_contents(e.a[1].obj_ea, -1, 0, STRCONV_ESCAPE))
for ea in Functions():
r += [e for e in find_expr(ea, query)]
for e in r:
print(e)
- get list of signed operators, display result in chooser
from idaapi import *
from hr_toolbox import ic_t
query = lambda cfunc, e: (e.op in
[hr.cot_asgsshr, hr.cot_asgsdiv,
hr.cot_asgsmod, hr.cot_sge,
hr.cot_sle, hr.cot_sgt,
hr.cot_slt, hr.cot_sshr,
hr.cot_sdiv, hr.cot_smod])
ic_t(query)
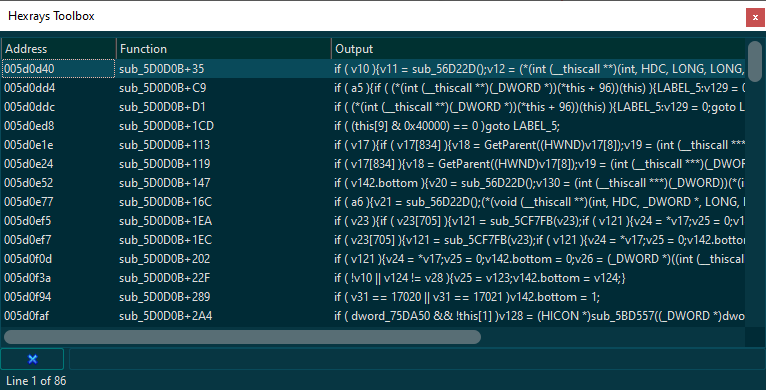
- get list of "if" statements, display result in chooser
from idaapi import *
from hr_toolbox import ic_t
ic_t(lambda cf, i: i.op is cit_if)
- get list of all loop statements in db, display result in chooser
from idaapi import *
from hr_toolbox import ic_t, query_db
ic_t(query_db(lambda cf,i: is_loop(i.op)))
- get list of loop constructs containing copy operations
from hr_toolbox import ic_t, query_db, find_child_expr
from ida_hexrays import *
find_copy_query = lambda cfunc, i: (i.op is cot_asg and
i.x.op is cot_ptr and
i.y.op is cot_ptr)
find_loop_query = lambda cfunc, i: (is_loop(i.op) and
find_child_expr(cfunc, i, find_copy_query))
ic_t(query_db(find_loop_query))
Note that the project description data, including the texts, logos, images, and/or trademarks,
for each open source project belongs to its rightful owner.
If you wish to add or remove any projects, please contact us at [email protected].