m0bilesecurity / Rms Runtime Mobile Security
Programming Languages
Projects that are alternatives of or similar to Rms Runtime Mobile Security
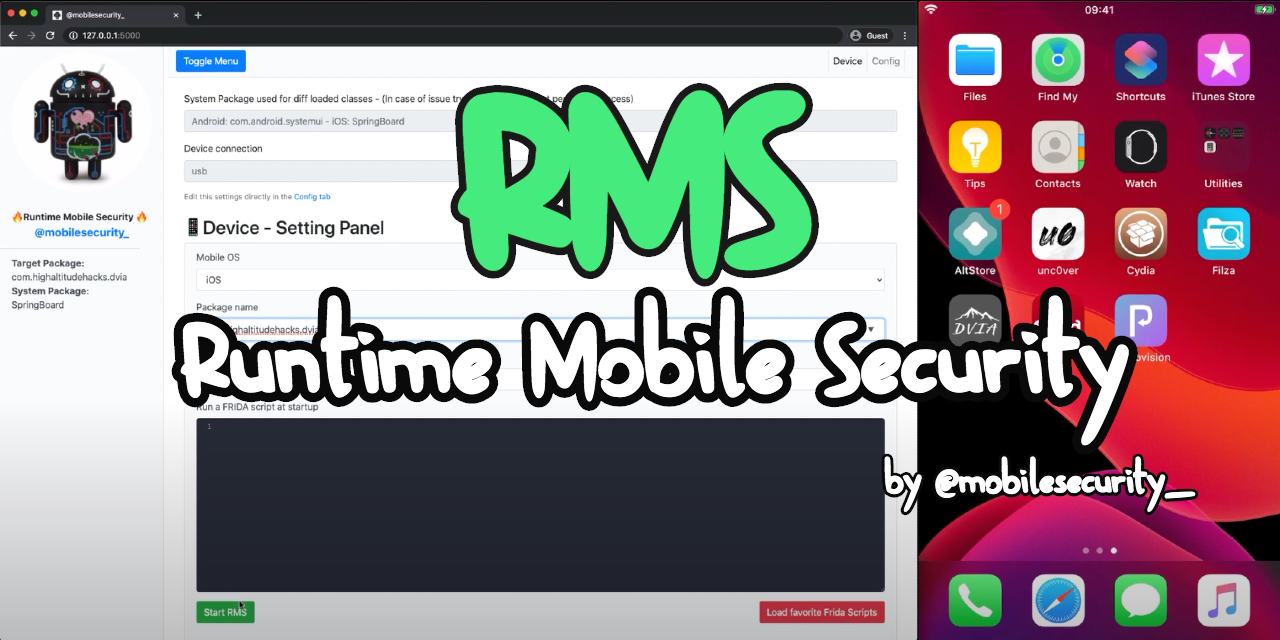
Runtime Mobile Security (RMS) 📱🔥
Runtime Mobile Security (RMS), powered by FRIDA, is a powerful web interface that helps you to manipulate Android and iOS Apps at Runtime.
With RMS you can easily dump all loaded classes and relative methods, hook everything on the fly, trace methods args and return value, load custom scripts and many other useful stuff.
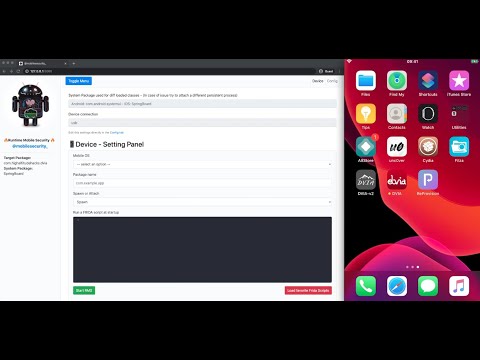
iOS DEMO - VIDEO
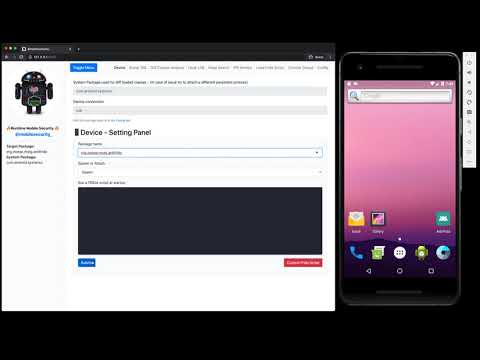
Android DEMO - VIDEO
Tutorial - Android
- Solving OWASP UnCrackable Android App Level 1 with Runtime Mobile Security (RMS)
- Solving OWASP UnCrackable Android App Level 2 with Runtime Mobile Security (RMS)
Prerequisites
- NodeJS installed on your computer
- FRIDA's CLI tools installed on your computer
- FRIDA server up and running on the target device
Quick smoke-test
As suggested by the official FRIDA doc, please perform a quick smoke-test to make sure FRIDA is working properly on your test device.
By running the frida-ps -U command from your desktop, you should receive the list of the processes running on your connected mobile device.
Android | iOS
PID NAME | PID NAME
1590 com.facebook.katana | 488 Clock
3282 com.twitter.android | 116 Facebook
… …
Tips
Some cool projects that can help you to auto install, update and run FRIDA on Android devices are:
They are not needed on iOS devices, since FRIDA starts just after the boot of the device (jailbreak mode).
Installation
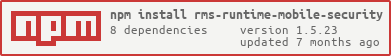
- Open the terminal and run the following command to install the npm package
npm install -g rms-runtime-mobile-security
- Make sure frida-server is up and running on the target device.
- Instructions are here: prerequisites / quick smoke-test
- Launch RMS via the following command
-
rms(orRMS-Runtime-Mobile-Security)
-
- Open your browser at
http://127.0.0.1:5000/ - Start enjoying RMS 📱🔥
Notes and possibile issues
- In case of issues with the npm package installed as a global cli app, please try the local installation (development mode)
- In case of issues with your favorite Browser (e.g. logs not printed in the web console), please use Google Chrome (fully supported)
- If RMS is not able to detect your device, please perform the following checks:
- double check if frida-server is up and running on the target device. Instructions are here: prerequisites / quick smoke-test
- RMS must be started after frida-server
- make sure that only 1 device is connected to your computer. RMS is currently not able to detect multiple devices
- kill RMS and start it again
Development mode
Follow the steps below if you want to develop new features for RMS 😉
git clone https://github.com/m0bilesecurity/RMS-Runtime-Mobile-Security.gitcd RMS-Runtime-Mobile-Security-
npm install(local installation) - Launch RMS via
node rms.js - You can also install RMS as global package by running the following commands:
-
npm install -gto install dependencies -
npm run compileto compile the frida-agent -
rmsto run RMS (anywhere)
-
NOTE: If you add new features to the agent (/agent/RMS_core.js), please remember to recompile the code by running npm run compile or directly via the frida-compile command (frida-compile agent/RMS_core.js -o agent/compiled_RMS_core.js)
General Info
Runtime Mobile Security (RMS) supports Android and iOS devices.
It has been tested on MacOS and with the following devices:
- AVD emulator
- Genymotion emulator
- Amazon Fire Stick 4K
- iPhone 7
- Chrome (Web Interface)
It should also work well on Windows and Linux but some minor adjustments may be needed.
Known issues and improvements
- Sometime RMS fails to load complex methods. Use a filter when this happens or feel free to improve the algo (agent/RMS_core.js)
- Socket are not working on Safari, please use Chrome instead
- RMS is not able to recognize multiple devices. Please do not connect more than one device at the same time
- Code is not optimized
- Feel free to send me your best JS script via a Pull Request. I'll be happy to bundle all the best as default scripts in the next RMS release (e.g. root detection bypass, ssl pinning, etc)
Usage
1. Run your favorite app by simply inserting its package name
NOTE RMS attachs a persistence process called com.android.systemui on Android and SpringBoard on iOS devices to get the list of all the classes that are already loaded in memory before the launch of the target app. If you have an issue with them, try to find a different default package that works well on your device. You can set another default package via the Config Tab or by simply editing the /config/config.json file.
2. Check which Classes and Methods have been loaded in memory
3. Hook on the fly Classes/Methods and trace their args and return values
Go back to the dump page in order to have an overview of all the hooked methods that have been executed by the app ✅
4. Search instances of a specific class on the Heap and call its methods
5. Select a Class and generate on the fly an Hook template for all its methods
6. Easily detect new classes that have been loaded in memory
7. Inject your favorite FRIDA CUSTOM SCRIPTS on the fly
Just add your .js files inside the custom_script folder and they will be automatically loaded by the web interface ready to be executed.
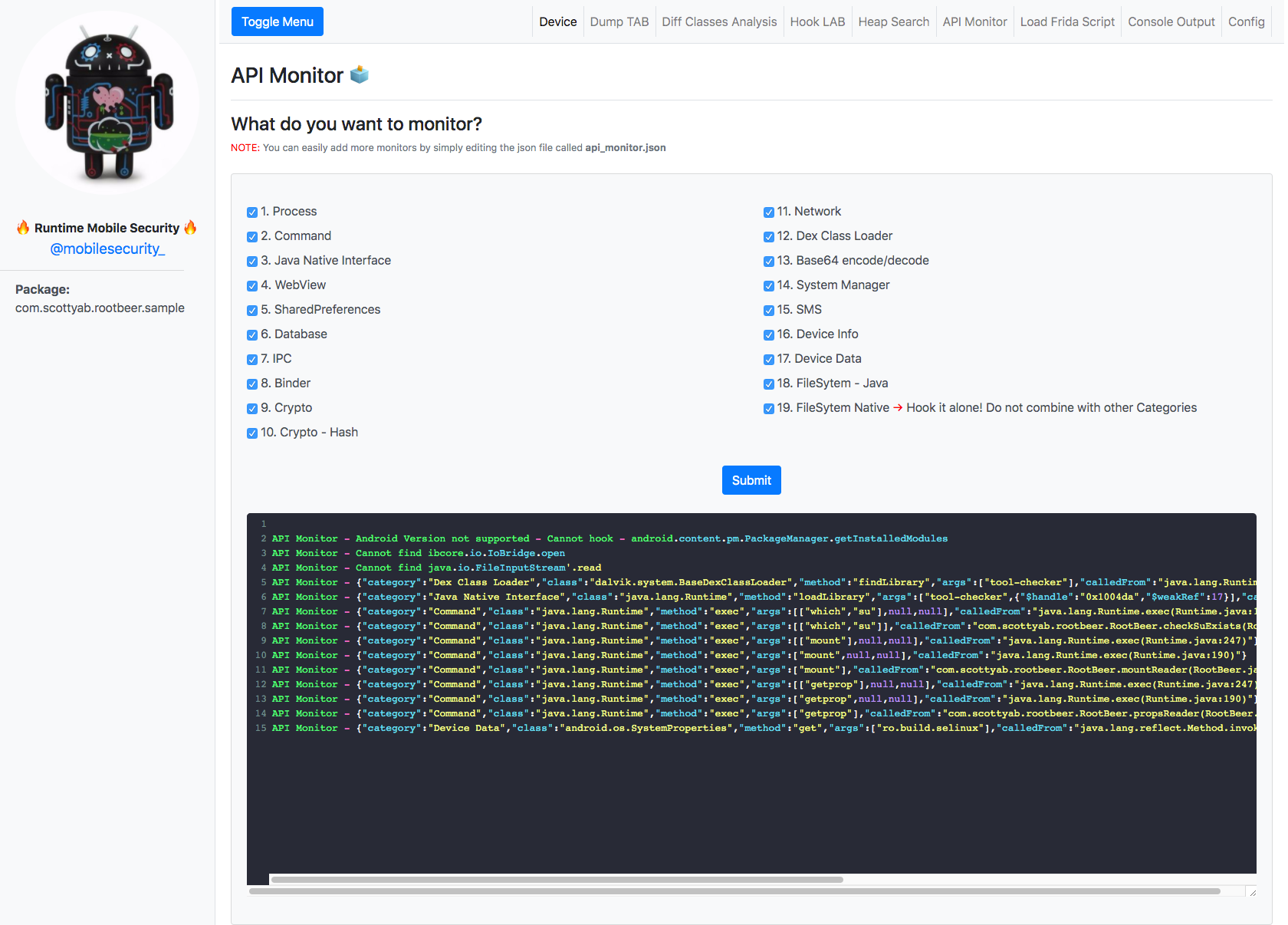
8. API Monitor - Android Only
via the API Monitor TAB you can easily monitor tons of Android APIs organized in 20 different Categories. Support can be easily extended by adding more classes/methods to the /config/api_monitor.json file.
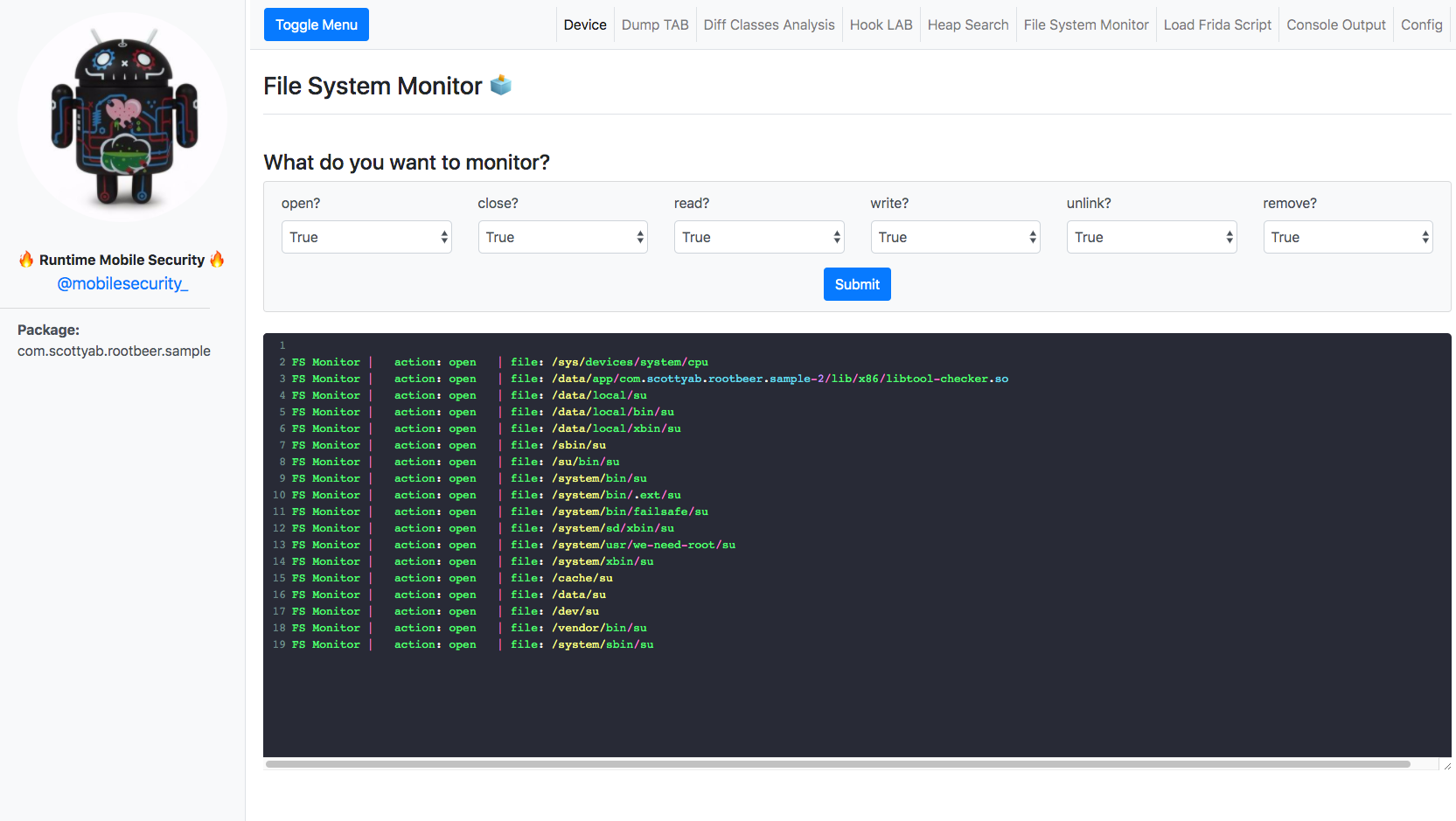
You can also monitor native functions: libc.so - open, close, read, write, unlink, remove
9. FRIDA Script to load Stetho by Facebook [BONUS]
Inject the FRIDA script to load the amazing Stetho.
Stetho is a sophisticated debug bridge for Android applications. When enabled, developers have access to the Chrome Developer Tools feature natively part of the Chrome desktop browser. Developers can also choose to enable the optional dumpapp tool which offers a powerful command-line interface to application internals.
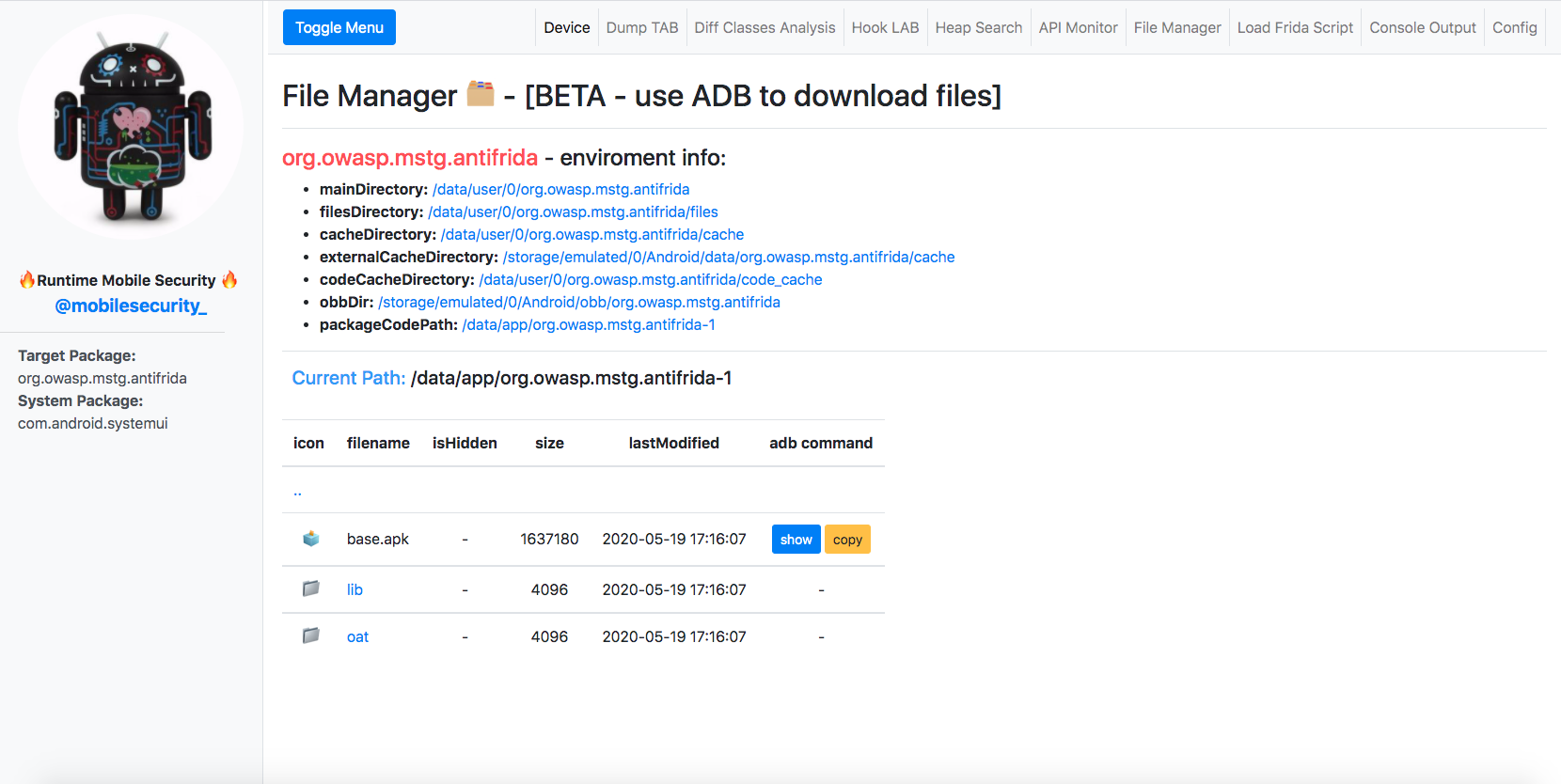
10. File Manager [BETA]
A simple File Manager has been implemented to help you exploring app's private folders and files. This feature is still in BETA.
improvement: frida-fs needs to be implemented to enable files download directly from the browser (File Manager TAB).
11. Static Analysis - iOS Only
Acknowledgements
Special thanks to the following Open Source projects for the inspiration:
FRIDA Custom Scripts bundled in RMS - Credits:
- Runtime Mobile Security (RMS)
- FSecureLABS
- Mediaservice
- federicodotta
- iddoeldor
- dzonerzy
- akabe1
- Areizen
- int3rf3r3nc3
- dki
- ay-kay
- chaitin
- lich4
- fadeevab
- realgam3
- noobpk
- enovella
DEMO apps:
- RootBeer Sample is the DEMO app used to show how RMS works. RootBeer is an amazing root detection library. I decided to use the Sample app as DEMO just to show that, as every client-side only check, its root detection logic can be easily bypassed if not combined with a server-side validation.
- DVIA a vulnerable app to test your iOS Penetration Testing Skills
- Anti-Frida Frida Detection Examples by Bernhard Mueller.
License
RMS is licensed under a GNU General Public v3 License.