orleven / Tentacle
Tentacle is a POC vulnerability verification and exploit framework. It supports free extension of exploits and uses POC scripts. It supports calls to zoomeye, fofa, shodan and other APIs to perform bulk vulnerability verification for multiple targets.
Stars: ✭ 258
Programming Languages
python
139335 projects - #7 most used programming language
Projects that are alternatives of or similar to Tentacle
Cerberus
A complete Grabber, sending data to a TCP server that you have to host and stocking all in a database.
Stars: ✭ 32 (-87.6%)
Mutual labels: poc
Shodan-RPi
A simple SSH bruteforce script targeting (not necessarily) Raspbian devices.
Stars: ✭ 13 (-94.96%)
Mutual labels: shodan
Pentesting
Misc. Public Reports of Penetration Testing and Security Audits.
Stars: ✭ 24 (-90.7%)
Mutual labels: poc
pentesting-multitool
Different utility scripts for pentesting and hacking.
Stars: ✭ 39 (-84.88%)
Mutual labels: shodan
Deep-Inside
Command line tool that allows you to explore IoT devices by using Shodan API.
Stars: ✭ 22 (-91.47%)
Mutual labels: shodan
chrome-spyware
Writing Spyware Made Easy - POC spyware Chrome Extension/Server
Stars: ✭ 25 (-90.31%)
Mutual labels: poc
ShonyDanza
A customizable, easy-to-navigate tool for researching, pen testing, and defending with the power of Shodan.
Stars: ✭ 86 (-66.67%)
Mutual labels: shodan
thelordseye
thelordseye searches and returns detailed information about devices that are directly connected to the internet [IoT] (Smart TV's, Fridges, Webcams, Traffic Lights etc).
Stars: ✭ 30 (-88.37%)
Mutual labels: shodan
mongodb-scraper
Scraps for publicly accessible MongoDB instances and dumps user passwords
Stars: ✭ 33 (-87.21%)
Mutual labels: shodan
awesome-list-of-secrets-in-environment-variables
🦄🔒 Awesome list of secrets in environment variables 🖥️
Stars: ✭ 538 (+108.53%)
Mutual labels: poc
CVE-2021-33766
ProxyToken (CVE-2021-33766) : An Authentication Bypass in Microsoft Exchange Server POC exploit
Stars: ✭ 37 (-85.66%)
Mutual labels: poc
Exploit-Development
Exploit Development - Weaponized Exploit and Proof of Concepts (PoC)
Stars: ✭ 84 (-67.44%)
Mutual labels: poc
DeepfakeHTTP
DeepfakeHTTP is a web server that uses HTTP dumps as a source for responses.
Stars: ✭ 373 (+44.57%)
Mutual labels: poc
Bluebox Ng
Pentesting framework using Node.js powers, focused in VoIP.
Stars: ✭ 255 (-1.16%)
Mutual labels: shodan
CVE-2018-7750
an RCE (remote command execution) approach of CVE-2018-7750
Stars: ✭ 18 (-93.02%)
Mutual labels: poc
NSE-scripts
NSE scripts to detect CVE-2020-1350 SIGRED and CVE-2020-0796 SMBGHOST, CVE-2021-21972, proxyshell, CVE-2021-34473
Stars: ✭ 105 (-59.3%)
Mutual labels: poc
Tentacle
.___________. _______ .__ __. .___________. ___ ______ __ _______
| || ____|| \ | | | | / \ / || | | ____| {1.0.0#stable}
`---| |----`| |__ | \| | `---| |----` / ^ \ | ,----'| | | |__
| | | __| | . ` | | | / /_\ \ | | | | | __|
| | | |____ | |\ | | | / _____ \ | `----.| `----.| |____
|__| |_______||__| \__| |__| /__/ \__\ \______||_______||_______| http://www.orleven.com
Tentacle is a POC vulnerability verification and exploit framework. It supports free extension of exploits and uses POC scripts. It supports calls to zoomeye, fofa, shodan and other APIs to perform bulk vulnerability verification for multiple targets. (Still in DEV...)
Install
pip3 install -r requestment.txt
Usage
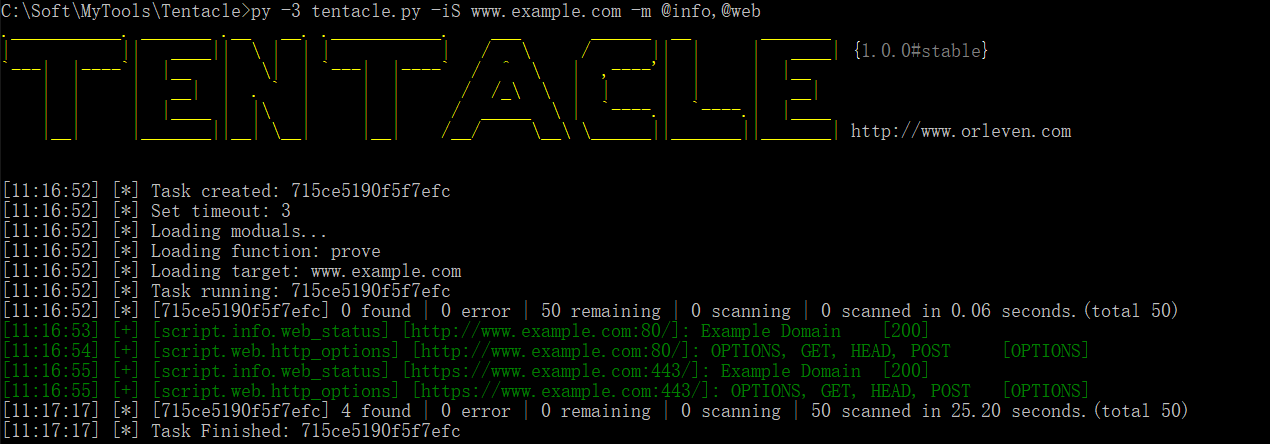
When you run it for the first time, the configuration file conf/tentacle.conf will be generated automatically.
# Show help for tentacle.
python3 tentacle.py --help
# Show all modules, and you can see it in `script` path.
python3 tentacle.py --show
# Show all function of modules by -f show or -f help
python3 tentacle.py -m script/web/web_status -f show
python3 tentacle.py -m script/web/web_status -f help
# Load target by iS/iN/iF/iT/iX/iE/gg/sd/ze/ff.
# Scan port and then it will try to send the poc.
python3 tentacle.py -m script/web/web_status -iS www.examples.com # Load target by url or host
python3 tentacle.py -m script/web/web_status -iN 192.168.111.0/24 # Load target by network
python3 tentacle.py -m script/web/web_status -iF target.txt # Load target by file
python3 tentacle.py -m script/web/web_status -iT dcc54c3e1cc2c2e1 # Load target by recode's target
python3 tentacle.py -m script/web/web_status -iX nmap_xml.xml # Load target by nmap.xml
python3 tentacle.py -m script/web/web_status -iE "powered by discuz" # Load target by baidu/bing/360so
python3 tentacle.py -m script/web/web_status -gg 'intext:powered by discuz' # Load target by google api
python3 tentacle.py -m script/web/web_status -sd 'apache' # Load target by shodan api
python3 tentacle.py -m script/web/web_status -ze 'app:weblogic' # Load target by zoomeye api
python3 tentacle.py -m script/web/web_status -ff 'domain="example.com"' # Load target by fofa api
# Load modules by -m (e.g. script/info/web_status,@web)
python3 tentacle.py -iS 127.0.0.1 -m script/web/web_status # Load web_status module
python3 tentacle.py -iS 127.0.0.1 -m @web # Load all module of web path
python3 tentacle.py -iS 127.0.0.1 -m script/web/web_status,@web # Load all module of web path and web_status module
python3 tentacle.py -iS 127.0.0.1 -m "*" # Load all module of script path
python3 tentacle.py -iS 127.0.0.1 -m "*" -e @web # Load all module of script path, exclude all module of web path
# Set port scan scope
python3 tentacle.py -iS 127.0.0.1 -m script/web/web_status # Scan top 150 ports and then perform bulk vulnerability verification for multiple targets.
python3 tentacle.py -iS 127.0.0.1 -m script/web/web_status -sP # Skip port scan and then it will try the default port number server
python3 tentacle.py -iS 127.0.0.1 -m script/web/web_status -lP 80-90,443 # Scan 80-90 ports and 443 port and then perform bulk vulnerability verification for multiple targets.
# Use function of modules by -m and -f (e.g. -m web_status -f prove), and you should make sure the function of module is exist.
python3 tentacle.py -m script/web/web_status -f prove
# Show task's result by -tS
python3 tentacle.py -tS 8d4b37597aaec25e
# Export task's result by -tS to test.xlsx
python3 tentacle.py -tS 8d4b37597aaec25e -o test
# Update by git
python3 tentacle.py --update
Update
- [2018-11-15] Code refactoring and fix bug.
- [2019-06-08] Code refactoring and add port scan.
- [2020-03-15] Code refactoring and add script.
Thanks
Note that the project description data, including the texts, logos, images, and/or trademarks,
for each open source project belongs to its rightful owner.
If you wish to add or remove any projects, please contact us at [email protected].