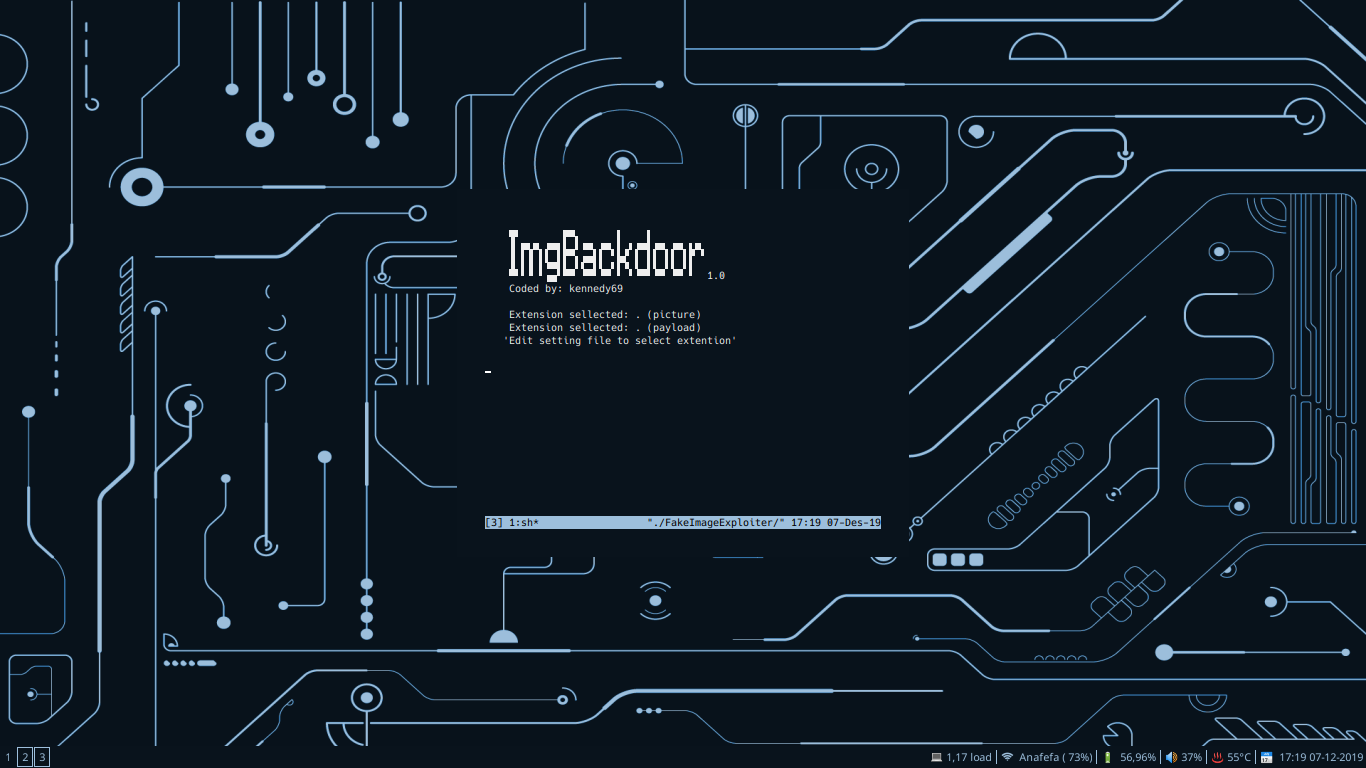
Tsuyoken / Imgbackdoor
Licence: apache-2.0
Hide your payload into .jpg file
Stars: ✭ 87
Programming Languages
shell
77523 projects
Projects that are alternatives of or similar to Imgbackdoor
Mouse
Mouse Framework is an iOS and macOS post-exploitation framework that gives you a command line session with extra functionality between you and a target machine using only a simple Mouse payload. Mouse gives you the power and convenience of uploading and downloading files, tab completion, taking pictures, location tracking, shell command execution, escalating privileges, password retrieval, and much more.
Stars: ✭ 186 (+113.79%)
Mutual labels: exploit, payload, backdoor, metasploit
Proton
Proton Framework is a Windows post-exploitation framework similar to other Windows post-exploitation frameworks. The major difference is that the Proton Framework does most of its operations using Windows Script Host, with compatibility in the core to support a default installation of Windows 2000 with no service packs all the way through Windows 10.
Stars: ✭ 142 (+63.22%)
Mutual labels: payload, backdoor, metasploit
Cloak
Cloak can backdoor any python script with some tricks.
Stars: ✭ 411 (+372.41%)
Mutual labels: exploit, payload, backdoor
Metasploit Cheat Sheet
Metasploit Cheat Sheet 💣
Stars: ✭ 139 (+59.77%)
Mutual labels: exploit, payload, metasploit
Entropy
Entropy Toolkit is a set of tools to provide Netwave and GoAhead IP webcams attacks. Entropy Toolkit is a powerful toolkit for webcams penetration testing.
Stars: ✭ 126 (+44.83%)
Mutual labels: exploit, payload, metasploit
Hackers Tool Kit
Its a framework filled with alot of options and hacking tools you use directly in the script from brute forcing to payload making im still adding more stuff i now have another tool out called htkl-lite its hackers-tool-kit just not as big and messy to see updates check on my instagram @tuf_unkn0wn or if there are any problems message me on instagram
Stars: ✭ 211 (+142.53%)
Mutual labels: exploit, payload, metasploit
Ms17 010 Python
MS17-010: Python and Meterpreter
Stars: ✭ 305 (+250.57%)
Mutual labels: payload, metasploit
A Red Teamer Diaries
RedTeam/Pentest notes and experiments tested on several infrastructures related to professional engagements.
Stars: ✭ 382 (+339.08%)
Mutual labels: exploit, metasploit
Xeexe Topantivirusevasion
Undetectable & Xor encrypting with custom KEY (FUD Metasploit Rat) bypass Top Antivirus like BitDefender,Malwarebytes,Avast,ESET-NOD32,AVG,... & Automatically Add ICON and MANIFEST to excitable
Stars: ✭ 387 (+344.83%)
Mutual labels: backdoor, metasploit
Hacktheworld
An Python Script For Generating Payloads that Bypasses All Antivirus so far .
Stars: ✭ 527 (+505.75%)
Mutual labels: backdoor, metasploit
Eternalblue
Eternalblue written in CSharp. Contains version detection, vulnerability scanner and exploit of MS17-010
Stars: ✭ 150 (+72.41%)
Mutual labels: exploit, metasploit
Pupy
Pupy is an opensource, cross-platform (Windows, Linux, OSX, Android) remote administration and post-exploitation tool mainly written in python
Stars: ✭ 6,737 (+7643.68%)
Mutual labels: payload, backdoor
Gray hat csharp code
This repository contains full code examples from the book Gray Hat C#
Stars: ✭ 301 (+245.98%)
Mutual labels: payload, metasploit
Remot3d
Remot3d: is a simple tool created for large pentesters as well as just for the pleasure of defacers to control server by backdoors
Stars: ✭ 263 (+202.3%)
Mutual labels: exploit, backdoor
Vegile
This tool will setting up your backdoor/rootkits when backdoor already setup it will be hidden your spesisifc process,unlimited your session in metasploit and transparent. Even when it killed, it will re-run again. There always be a procces which while run another process,So we can assume that this procces is unstopable like a Ghost in The Shell
Stars: ✭ 478 (+449.43%)
Mutual labels: backdoor, metasploit
Tegrarcmgui
C++ GUI for TegraRcmSmash (Fusée Gelée exploit for Nintendo Switch)
Stars: ✭ 965 (+1009.2%)
Mutual labels: exploit, payload
V3n0m Scanner
Popular Pentesting scanner in Python3.6 for SQLi/XSS/LFI/RFI and other Vulns
Stars: ✭ 847 (+873.56%)
Mutual labels: exploit, metasploit
Pysploit
Remote exploitation framework written in Python
Stars: ✭ 37 (-57.47%)
Mutual labels: exploit, payload
_____ ____ _ _
|_ _| | _ \ | | | |
| | _ __ ___ __ _| |_) | __ _ ___| | ____| | ___ ___ _ __
| | | '_ ` _ \ / _` | _ < / _` |/ __| |/ / _` |/ _ \ / _ \| '__|
_| |_| | | | | | (_| | |_) | (_| | (__| < (_| | (_) | (_) | |
|_____|_| |_| |_|\__, |____/ \__,_|\___|_|\_\__,_|\___/ \___/|_|
__/ |
|___/
Version release: v1.0 (Stable)
Author: Ferdi S Kennedy [ kennedy69 ]
Distros Supported : Linux Ubuntu, Kali, Mint, Parrot OS
Legal Disclamer:
The author does not hold any responsibility for the bad use of this tool,
remember that attacking targets without prior consent is illegal and punished by law.
Description:
This module takes one existing image.jpg and one payload.ps1 (input by user) and
builds a new payload (agent.jpg.exe) that if executed it will trigger the download of
the 2 previous files stored into apache2 (image.jpg + payload.ps1) and execute them.
This module also changes the agent.exe Icon to match one file.jpg Then uses the spoof
'Hide extensions for known file types' method to hidde the agent.exe extension.
All payloads (user input) will be downloaded from our apache2 webserver
and executed into target RAM. The only extension (payload input by user)
that requires to write payload to disk are .exe binaries.
Exploitation:
ImgBackdoor stores all files in apache2 webroot, zips (.zip) the agent,
starts apache2 and metasploit services(handler), and provides a URL to send to
target (triggers agent.zip download). As soon as the victim runs our executable,
our picture will be downloaded and opened in the default picture viewer, our
malicious payload will be executed, and we will get a meterpreter session.
But it also stores the agent (not ziped) into ImgBackdoor/output folder
if we wish to deliver agent.jpg.exe using another diferent attack vector.
'This tool also builds a cleaner.rc file to delete payloads left in target'
Payloads accepted (user input):
payload.ps1 (default) | payload.bat | payload.txt | payload.exe [Metasploit]
"Edit 'settings' file before runing tool to use other extensions"
Pictures accepted (user input):
All pictures with .jpg (default) | .jpeg | .png extensions (all sizes)
"Edit 'settings' file before runing tool to use other extensions"
Dependencies/Limitations:
xterm, zenity, apache2, mingw32[64], ResourceHacker(wine)
'Auto-Installs ResourceHacker.exe under ../.wine/Program Files/.. directorys'
WARNING: To change icon manually (resource hacker bypass) edit 'settings' file.
WARNING: Only under windows systems the 2º extension will be hidden (so zip it)
WARNING: The agent.jpg.exe requires the inputed files to be in apache2 (local lan hack)
WARNING: The agent.jpg.exe uses the powershell interpreter (does not work againts wine).
WARNING: This tool will not accept payload (user input) arguments (eg nc.exe -lvp 127.0.0.1 555)
WARNING: The ResourceHacker provided by this tool requires WINE to be set to windows 7
Another senarios:
If you wish to use your own binary (user input - not metasploit payloads) then:
1 - Edit 'settings' file before runing tool and select 'NON_MSF_PAYLOADS=YES' 2 - Select the binary extension to use 'Remmenber to save settings file before continue' ..
3 - Run ImgBackdoor to metamorphosis your binary (auto-storage all files in apache) .. 4 - Open new terminal and execute your binary handler to recibe connection. HINT: This funtion will NOT build a cleaner.rc
The noob friendly funtion:
Bypass the need to input your payload.ps1, And let ImgBackdoor take
care of building the required payload.ps1 + agent.jpg.exe and config the handler.
"With this funtion active, you only need to input your picture.jpg :D"
Select the binary extension to use
HINT: This funtion allow users to build (ps1|bat|txt) payloads
HINT: This funtion will NOT build .exe binaries
"WINE is not owned by you":
If you get this message it means that you are executing ImgBackdoor
as sudo and your wine installation belongs to user (is not owned by you) to
bypass this issue just execute ImgBackdoor as the wine owner.
EXAMPLE: If wine its owned by spirited_wolf, execute tool without sudo
EXAMPLE: If wine its owned by root, execute tool as sudo
Download/Install/Config:
1 - Download framework from github
git clone https://github.com/kennedy69/ImgBackdoor
2 - Set files execution permitions
cd ImgBackdoor
sudo chmod +x *.sh
3 - Config ImgBackdoor settings
nano settings
4 - Run main tool
sudo ./ImgBackdoor
WARNING: set Resource-Hacker.exe installer to 'Program Files' (not Program Files (x86))
Note that the project description data, including the texts, logos, images, and/or trademarks,
for each open source project belongs to its rightful owner.
If you wish to add or remove any projects, please contact us at [email protected].