reb311ion / Rebel Framework
Licence: gpl-3.0
Advanced and easy to use penetration testing framework 💣🔎
Stars: ✭ 183
Programming Languages
python
139335 projects - #7 most used programming language
Labels
Projects that are alternatives of or similar to Rebel Framework
Rapidscan
🆕 The Multi-Tool Web Vulnerability Scanner.
Stars: ✭ 775 (+323.5%)
Mutual labels: kali-linux, security-tools, reconnaissance, vulnerability-scanners, vulnerability-detection, vulnerability-assessment
Hellraiser
Vulnerability scanner using Nmap for scanning and correlating found CPEs with CVEs.
Stars: ✭ 413 (+125.68%)
Mutual labels: hacking, security-tools, vulnerability-scanners, vulnerability-detection, vulnerability-assessment
Pentesting toolkit
🏴☠️ Tools for pentesting, CTFs & wargames. 🏴☠️
Stars: ✭ 1,268 (+592.9%)
Mutual labels: hacking, ctf, forensics, reverse-engineering
Replica
Ghidra Analysis Enhancer 🐉
Stars: ✭ 194 (+6.01%)
Mutual labels: decompiler, security-tools, malware-analysis, reverse-engineering
Infosec reference
An Information Security Reference That Doesn't Suck; https://rmusser.net/git/admin-2/Infosec_Reference for non-MS Git hosted version.
Stars: ✭ 4,162 (+2174.32%)
Mutual labels: hacking, forensics, information-security, reverse-engineering
Lynis
Lynis - Security auditing tool for Linux, macOS, and UNIX-based systems. Assists with compliance testing (HIPAA/ISO27001/PCI DSS) and system hardening. Agentless, and installation optional.
Stars: ✭ 9,137 (+4892.9%)
Mutual labels: security-tools, vulnerability-scanners, vulnerability-detection, vulnerability-assessment
Nerve
NERVE Continuous Vulnerability Scanner
Stars: ✭ 267 (+45.9%)
Mutual labels: security-tools, vulnerability-scanners, vulnerability-detection, vulnerability-assessment
Awesome Hacking Resources
A collection of hacking / penetration testing resources to make you better!
Stars: ✭ 11,466 (+6165.57%)
Mutual labels: hacking, ctf, mitm, reverse-engineering
Xattacker
X Attacker Tool ☣ Website Vulnerability Scanner & Auto Exploiter
Stars: ✭ 897 (+390.16%)
Mutual labels: hacking, security-tools, vulnerability-detection, vulnerability-assessment
Vulnx
vulnx 🕷️ is an intelligent bot auto shell injector that detect vulnerabilities in multiple types of cms { `wordpress , joomla , drupal , prestashop .. `}
Stars: ✭ 1,009 (+451.37%)
Mutual labels: hacking, security-tools, vulnerability-detection, vulnerability-assessment
Vuls
Agent-less vulnerability scanner for Linux, FreeBSD, Container, WordPress, Programming language libraries, Network devices
Stars: ✭ 8,844 (+4732.79%)
Mutual labels: security-tools, vulnerability-scanners, vulnerability-detection, vulnerability-assessment
H4cker
This repository is primarily maintained by Omar Santos and includes thousands of resources related to ethical hacking / penetration testing, digital forensics and incident response (DFIR), vulnerability research, exploit development, reverse engineering, and more.
Stars: ✭ 10,451 (+5610.93%)
Mutual labels: hacking, vulnerability-scanners, vulnerability-assessment
Antidebugging
A collection of c++ programs that demonstrate common ways to detect the presence of an attached debugger.
Stars: ✭ 161 (-12.02%)
Mutual labels: hacking, malware-analysis, reverse-engineering
Vulscan
Advanced vulnerability scanning with Nmap NSE
Stars: ✭ 2,305 (+1159.56%)
Mutual labels: vulnerability-scanners, vulnerability-detection, vulnerability-assessment
Patrowldocs
PatrOwl - Open Source, Free and Scalable Security Operations Orchestration Platform
Stars: ✭ 105 (-42.62%)
Mutual labels: security-tools, vulnerability-scanners, vulnerability-detection
Vailyn
A phased, evasive Path Traversal + LFI scanning & exploitation tool in Python
Stars: ✭ 103 (-43.72%)
Mutual labels: vulnerability-scanners, vulnerability-detection, vulnerability-assessment
Gda Android Reversing Tool
GDA is a new fast and powerful decompiler in C++(working without Java VM) for the APK, DEX, ODEX, OAT, JAR, AAR, and CLASS file. which supports malicious behavior detection, privacy leaking detection, vulnerability detection, path solving, packer identification, variable tracking, deobfuscation, python&java scripts, device memory extraction, dat…
Stars: ✭ 2,332 (+1174.32%)
Mutual labels: decompiler, malware-analysis, vulnerability-scanners
Awesome Hacking
Awesome hacking is an awesome collection of hacking tools.
Stars: ✭ 1,802 (+884.7%)
Mutual labels: hacking, security-tools, forensics
Raccoon
A high performance offensive security tool for reconnaissance and vulnerability scanning
Stars: ✭ 2,312 (+1163.39%)
Mutual labels: hacking, reconnaissance, vulnerability-assessment
Purify
All-in-one tool for managing vulnerability reports from AppSec pipelines
Stars: ✭ 72 (-60.66%)
Mutual labels: security-tools, vulnerability-scanners, vulnerability-assessment
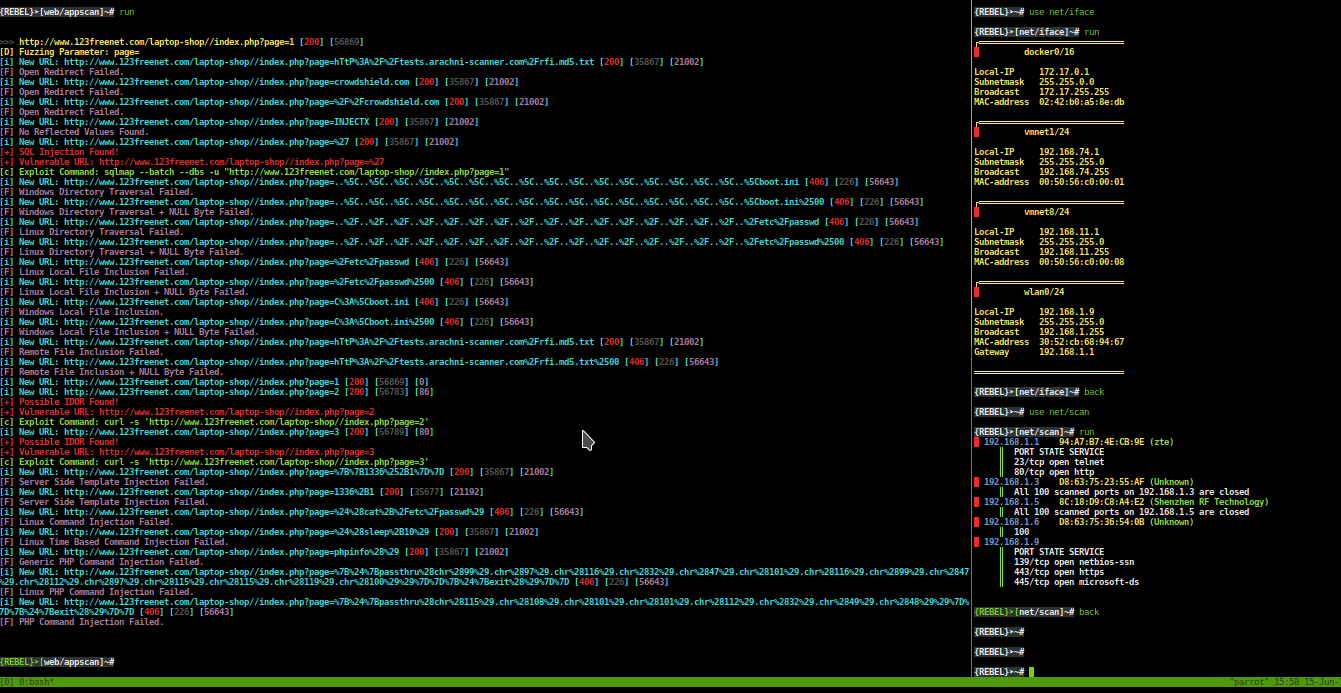
REBEL-FRAMEWORK
START
git clone https://github.com/rebellionil/rebel-framework.git
cd rebel-framework
bash setup.sh
bash rebel.sh
MODULES
SCREENSHOTS
DEMOS
SUPPORTED DISTRIBUTIONS
| Distribution | Version Check | supported | dependencies already installed | status |
|---|---|---|---|---|
| Kali Linux | 4.4.0 | yes | yes | working |
| Parrot OS | 4.14.0 | yes | yes | working |
PORT YOUR OWN TOOLS TO REBEL !
- scan.py
┌─[[email protected]]─[~]
└──╼ #python scan.py -h
-h --help print usage
usage ./scan.py <target>
- controller.sh sample
#!/bin/bash
normal='\e[0m'
arr[0]='\e[1;94m' ; blue=${arr[0]}
arr[1]='\e[1;31m' ; red=${arr[1]}
arr[2]='\e[1;33m' ; yellow=${arr[2]}
arr[3]='\e[1;35m' ; purp=${arr[3]}
arr[4]='\e[1;32m' ; green=${arr[4]}
arr[5]='\e[97m' ; white=${arr[5]}
grayterm='\e[1;40m'
module=$(echo $1 | cut -d '/' -f 2 )
if [[ $module != "scan" ]] ; then
echo -e "${red}[x] Wrong module name"
exit
fi
misc(){
if [[ $1 == "back" ]] || [[ $1 == "exit" ]] || [[ $1 == "quit" ]] ; then
exit
elif [[ $1 == '!' ]] ; then
$2
elif [[ $1 == "clear" ]] || [[ $1 == "reset" ]] ; then
clear
elif [[ $1 == "help" ]] || [[ $1 == "?" ]] ; then
bash print_help_modules.sh help
elif [[ $1 == "banner" ]] ; then
rand="$[ $RANDOM % 6 ]"
color="${arr[$rand]}" # select random color
echo -e $color
python print_banner.py
elif [[ $1 == "" ]] ; then
:
else
echo -e "${purp}[-] Invalid parameter use show 'help' for more information"
fi
}
target="site.com"
while IFS= read -e -p "$( echo -e $white ; echo -e ${grayterm}{REBEL}➤[${white}$1]~#${normal} ) " cmd1 ; do
history -s "$cmd1"
if [[ ${1} =~ 're/' ]] ; then
if [[ $( echo $cmd1 | cut -d " " -f 1 ) == "show" ]] ; then
if [[ $( echo $cmd1 | cut -d " " -f 2 ) == "options" ]] ; then
{
echo -e " Option\t\t\t\t|Value"
echo -e " ======\t\t\t\t|====="
echo -e " target\t\t\t\t|$target"
} | column -t -s "|"
elif [[ $( echo $cmd1 | cut -d " " -f 2 ) == "modules" ]] ; then
bash print_help_modules.sh modules
elif [[ $( echo $cmd1 | cut -d " " -f 2 ) == "help" ]] ; then
bash print_help_modules.sh help
fi
elif [[ $( echo $cmd1 | cut -d " " -f 1 ) == 'set' ]] ; then
if [[ $( echo $cmd1 | cut -d " " -f 2 ) == 'target' ]] ; then
target=$( echo $cmd1 | cut -d " " -f 3- | sed "s/'//g")
fi
elif [[ $( echo $cmd1 | cut -d " " -f 1 ) == 'run' ]] ; then
python scan.py $target
else
misc $cmd1
fi
fi
done
BUG ?
OPEN NEW ISSUE
https://github.com/rebellionil/rebel-framework/issues
TODO
- [ ] Add wireless modules
- [ ] Add memory forensics modules
- [ ] Add java and pyc decompilers
- [ ] Make rebel scriptable and add command line arguments
- [ ] Add bruteforce modules
DONATE
| COIN | ADDRESS |
|---|---|
| ETH | 0x46409ba4e86313d99a5e13DD1Ca5f82d95529553 |
| BTC | 11wqnCon1V3NmYGbkLtZtAWaqbH3Nc3VS |
EXTERNAL PROJECTS USED INSIDE THE FRAMEWORK
https://github.com/rebe11ion/tornado
https://github.com/rebe11ion/CryptNote
https://github.com/1N3/BlackWidow
https://github.com/Dionach/CMSmap
https://github.com/vincepare/DirScan
https://github.com/s0md3v/Decodify
https://github.com/UndeadSec/SocialFish
https://github.com/evait-security/weeman
https://github.com/m4ll0k/Infoga
https://github.com/Moham3dRiahi/Th3inspector
https://github.com/sdushantha/qr-filetransfer
- special thanks for Mahmoud Mohamed for helping improve the project quality by testing it in several environments.
© 2018
Note that the project description data, including the texts, logos, images, and/or trademarks,
for each open source project belongs to its rightful owner.
If you wish to add or remove any projects, please contact us at [email protected].