yeggor / Uefi_retool
Licence: mit
A tool for UEFI firmware reverse engineering
Stars: ✭ 227
Programming Languages
python
139335 projects - #7 most used programming language
Projects that are alternatives of or similar to Uefi retool
Efixplorer
IDA plugin for UEFI firmware analysis and reverse engineering automation
Stars: ✭ 268 (+18.06%)
Mutual labels: ida-plugin, firmware, uefi, reverse-engineering
Stingray
IDAPython plugin for finding function strings recursively
Stars: ✭ 110 (-51.54%)
Mutual labels: ida-plugin, idapython, reverse-engineering
Efiseek
Ghidra analyzer for UEFI firmware.
Stars: ✭ 45 (-80.18%)
Mutual labels: firmware, uefi, reverse-engineering
Flare Ida
IDA Pro utilities from FLARE team
Stars: ✭ 1,374 (+505.29%)
Mutual labels: ida-plugin, idapython, reverse-engineering
Scratchabit
Easily retargetable and hackable interactive disassembler with IDAPython-compatible plugin API
Stars: ✭ 369 (+62.56%)
Mutual labels: ida-plugin, idapython, reverse-engineering
Sark
IDAPython Made Easy
Stars: ✭ 477 (+110.13%)
Mutual labels: ida-plugin, idapython, reverse-engineering
Ghidra Firmware Utils
Ghidra utilities for analyzing PC firmware
Stars: ✭ 194 (-14.54%)
Mutual labels: firmware, uefi, reverse-engineering
Idarling
Collaborative Reverse Engineering plugin for IDA Pro & Hex-Rays
Stars: ✭ 588 (+159.03%)
Mutual labels: ida-plugin, idapython, reverse-engineering
Awesome Reverse Engineering
Reverse Engineering Resources About All Platforms(Windows/Linux/macOS/Android/iOS/IoT) And Every Aspect! (More than 3500 open source tools and 2300 posts&videos)
Stars: ✭ 2,954 (+1201.32%)
Mutual labels: ida-plugin, idapython, reverse-engineering
Mazewalker
Toolkit for enriching and speeding up static malware analysis
Stars: ✭ 132 (-41.85%)
Mutual labels: idapython, reverse-engineering
Classinformer Ida7
ClassInformer backported for IDA Pro 7.0
Stars: ✭ 226 (-0.44%)
Mutual labels: ida-plugin, reverse-engineering
Amie
A Minimalist Instruction Extender for the ARM architecture and IDA Pro
Stars: ✭ 136 (-40.09%)
Mutual labels: idapython, reverse-engineering
Rematch
REmatch, a complete binary diffing framework that is free and strives to be open source and community driven.
Stars: ✭ 141 (-37.89%)
Mutual labels: ida-plugin, reverse-engineering
Lighthouse
A Code Coverage Explorer for Reverse Engineers
Stars: ✭ 1,348 (+493.83%)
Mutual labels: idapython, reverse-engineering
Jarvis
"Just Another ReVersIng Suite" or whatever other bullshit you can think of
Stars: ✭ 137 (-39.65%)
Mutual labels: ida-plugin, reverse-engineering
Ida Batch decompile
*Decompile All the Things* - IDA Batch Decompile plugin and script for Hex-Ray's IDA Pro that adds the ability to batch decompile multiple files and their imports with additional annotations (xref, stack var size) to the pseudocode .c file
Stars: ✭ 198 (-12.78%)
Mutual labels: ida-plugin, reverse-engineering
UEFI_RETool
A tool for UEFI firmware reverse engineering.
Table of Contents
Click to open TOC
UEFI firmware analysis with uefi_retool.py script
Usage:
- Copy
ida_plugin/uefi_analyser.pyscript andida_plugin/uefi_analyserdirectory to IDA plugins directory - Edit
config.jsonfile-
PE_DIRis a directory that contains all executable images from the UEFI firmware -
DUMP_DIRis a directory that contains all components from the firmware filesystem -
LOGS_DIRis a directory for logs -
IDA_PATHandIDA64_PATHare paths to IDA Pro executable files
-
- Run
pip install -r requirements.txt - Run
python uefi_retool.pycommand to display the help message
Commands
python uefi_retool.py
Usage: uefi_retool.py [OPTIONS] COMMAND [ARGS]...
Options:
--help Show this message and exit.
Commands:
get-images Get executable images from UEFI firmware.
get-info Analyze the entire UEFI firmware.
get-pp Get a list of proprietary protocols in the UEFI firmware.
get-images
python uefi_retool.py get-images --help
Usage: uefi_retool.py get-images [OPTIONS] FIRMWARE_PATH
Get executable images from UEFI firmware. Images are stored in "modules"
directory.
Options:
--help Show this message and exit.
Example:
python uefi_retool.py get-images test_fw/fw-tp-x1-carbon-5th.bin
get-info
python uefi_retool.py get-info --help
Usage: uefi_retool.py get-info [OPTIONS] FIRMWARE_PATH
Analyze the entire UEFI firmware. The analysis result is saved to .json
file.
Options:
-w, --workers INTEGER Number of workers (8 by default).
--help Show this message and exit.
Example:
python uefi_retool.py get-info -w 6 test_fw/fw-tp-x1-carbon-5th.bin
get-pp
python uefi_retool.py get-pp --help
Usage: uefi_retool.py get-pp [OPTIONS] FIRMWARE_PATH
Get a list of proprietary protocols in the UEFI firmware. The result is
saved to .json file.
Options:
-w, --workers INTEGER Number of workers (8 by default).
--help Show this message and exit.
Example:
python uefi_retool.py get-pp -w 6 test_fw/fw-tp-x1-carbon-5th.bin
Additional tools
-
tools/update_edk2_guids.pyis a script that updates protocol GUIDs list fromedk2project
IDA plugin
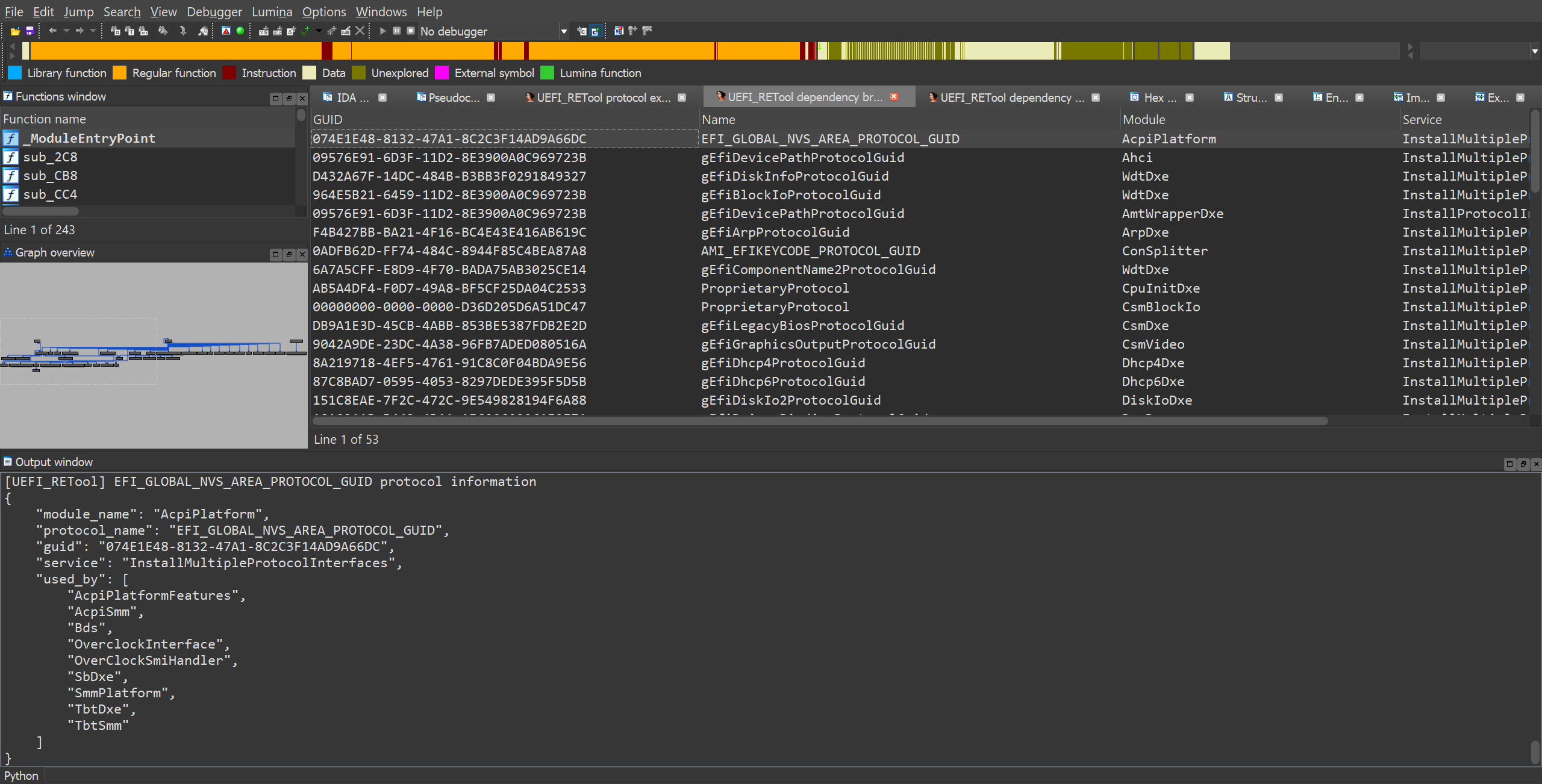
Analyser & Protocol explorer
Usage
-
Copy
uefi_analyseranduefi_analyser.pyto your%IDA_DIR%/pluginsdirectory -
Open the executable UEFI image in IDA and go to
Edit->Plugins->UEFI analyser(alternatively, you can use the key combinationCtrl+Alt+U)
Example
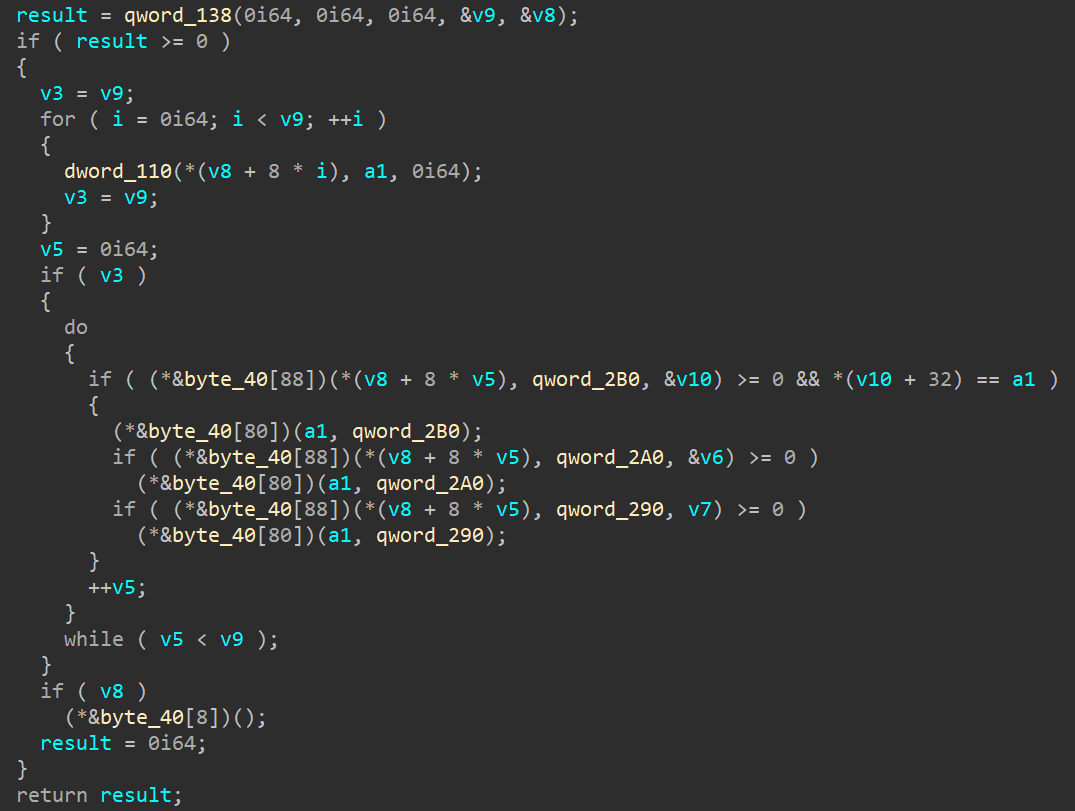
Before analysis
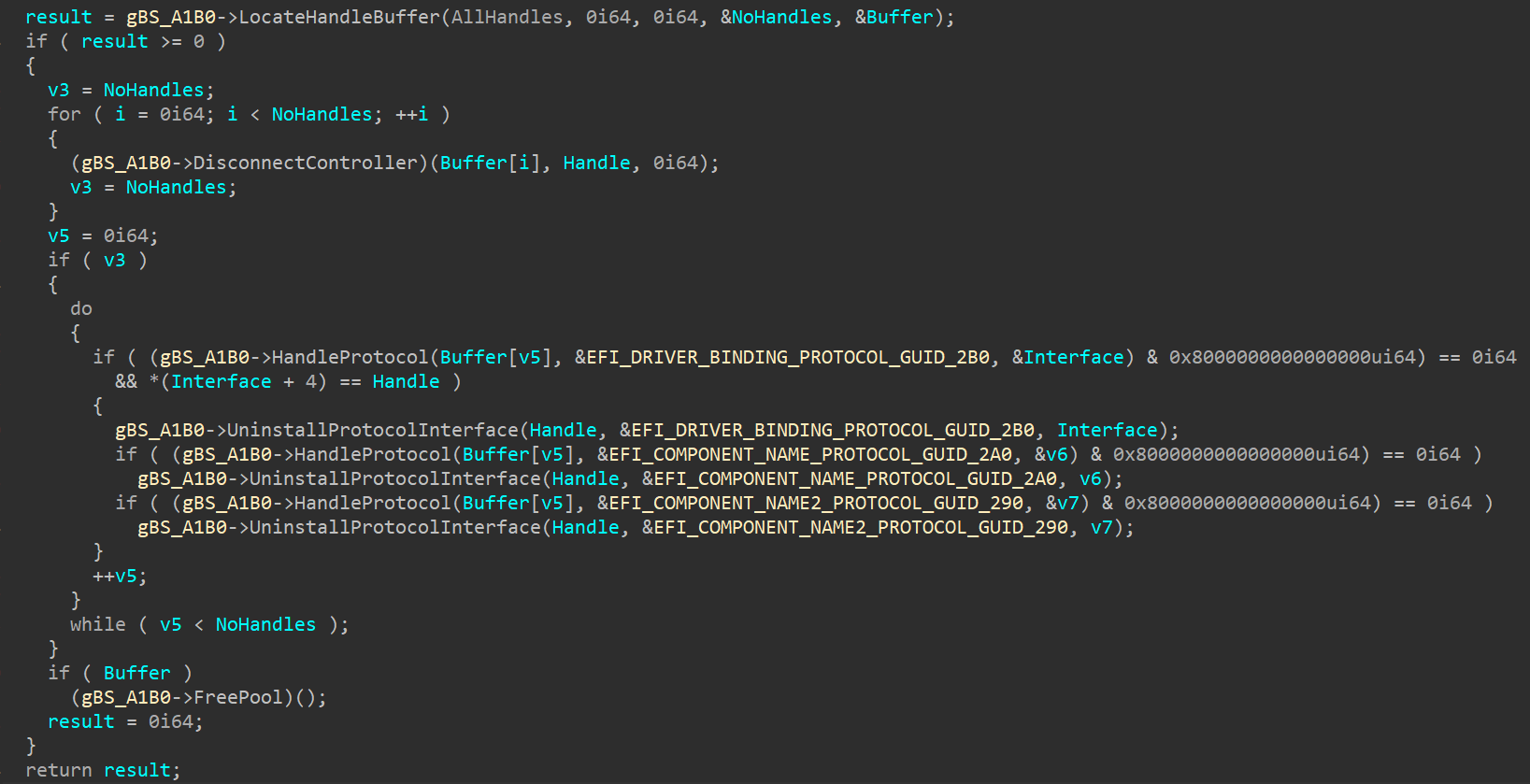
After analysis
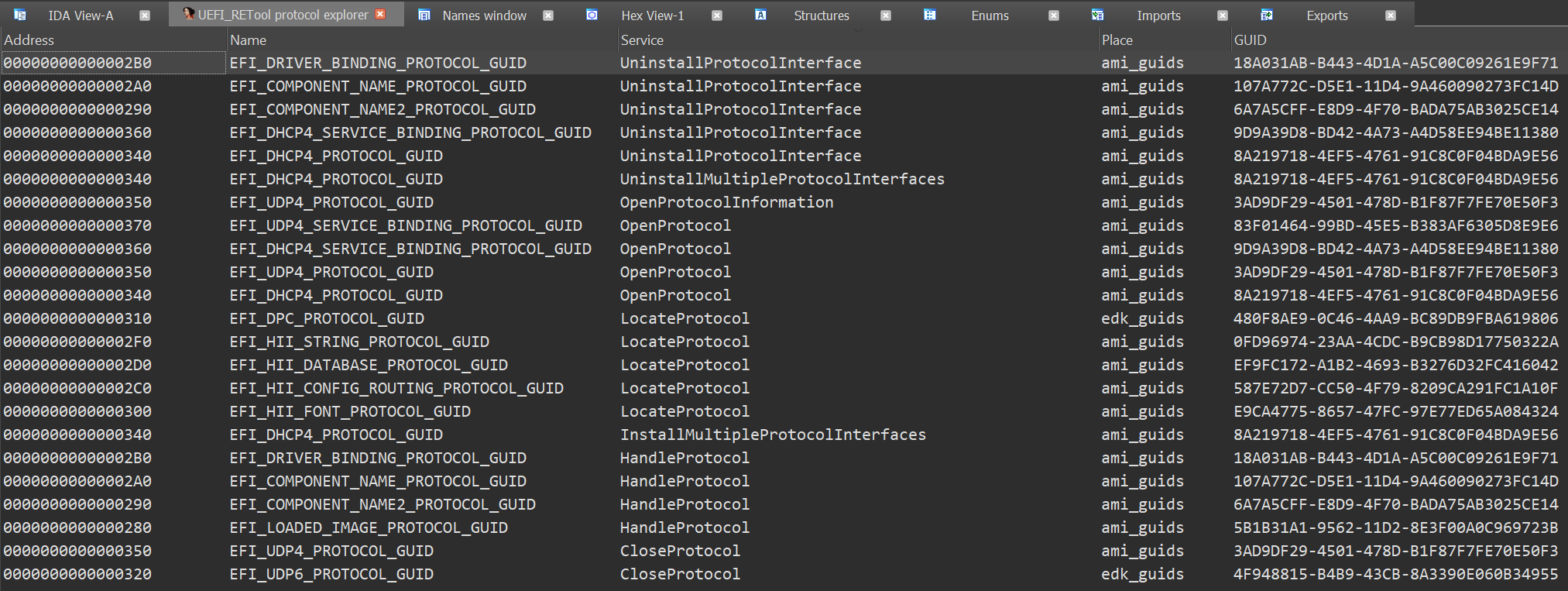
Protocol explorer window
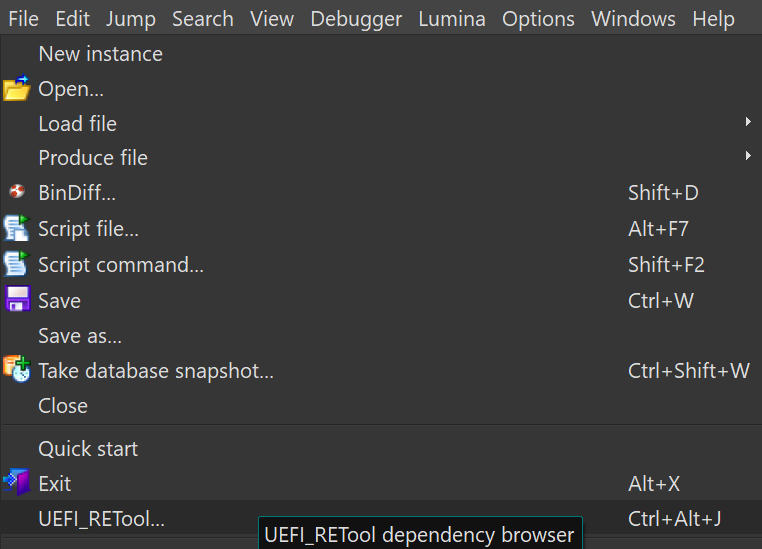
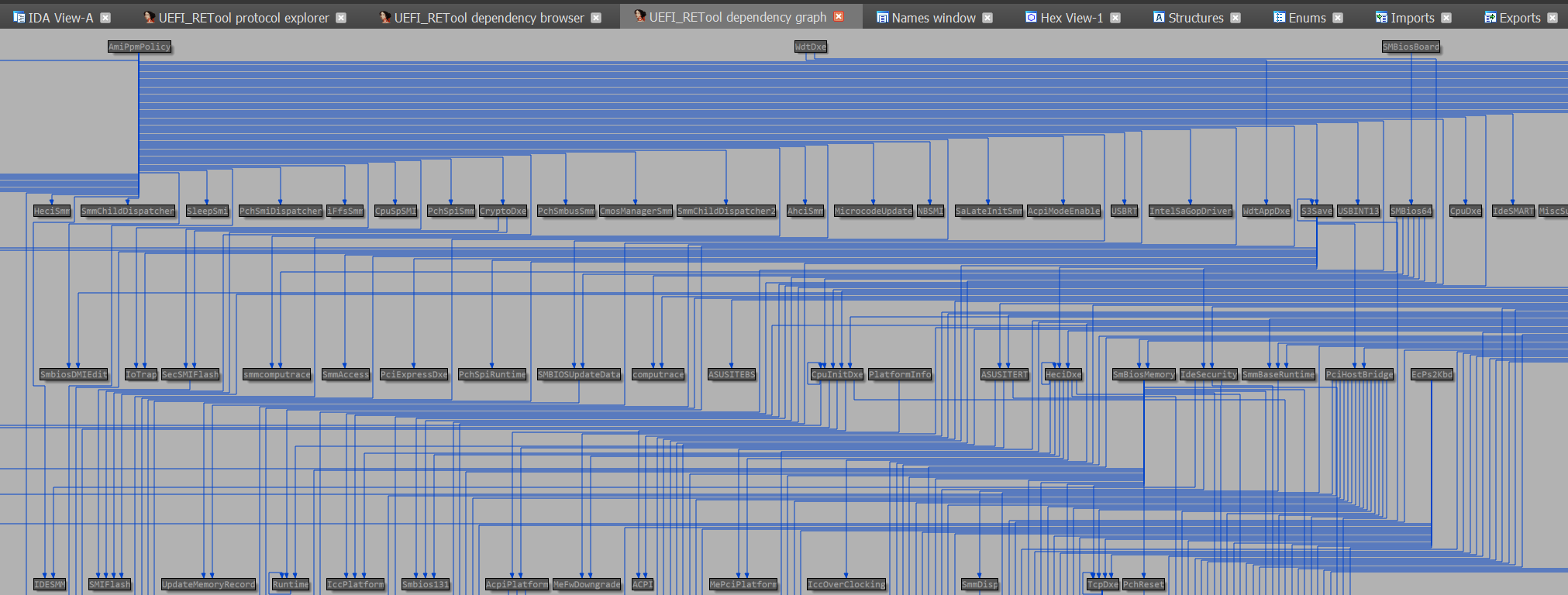
Dependency browser & Dependency graph
Usage
-
Analyse the firmware using uefi_retool.py
python uefi_retool.py get-info FIRMWARE_PATH
-
Load
<LOGS_DIR>/<FIRMWARE_NAME>-all-info.jsonfile to IDA (File->UEFI_RETool...)alternatively, you can use the key combination
Ctrl+Alt+J)
Example
Dependency browser window
Dependency graph
Similar works
Note that the project description data, including the texts, logos, images, and/or trademarks,
for each open source project belongs to its rightful owner.
If you wish to add or remove any projects, please contact us at [email protected].