gitgiter / Graph Adversarial Learning
Licence: gpl-3.0
A curated collection of adversarial attack and defense on graph data.
Stars: ✭ 188
Projects that are alternatives of or similar to Graph Adversarial Learning
Awesome Design Patterns
A curated list of software and architecture related design patterns.
Stars: ✭ 15,579 (+8186.7%)
Mutual labels: resources
You Dont Need Gui
Stop relying on GUI; CLI **ROCKS**
Stars: ✭ 4,766 (+2435.11%)
Mutual labels: resources
Google Mobile Web Specialist Certification Guide
If you are looking for becoming a Mobile Web Specialist by Google, this guide will be your best friend in your journey
Stars: ✭ 183 (-2.66%)
Mutual labels: resources
Women In Technology
A collection of resources for women in tech, consisting of - courses, learning guides, amazing sites and repos, blogs, programs and events. scholarships, etc.
Stars: ✭ 170 (-9.57%)
Mutual labels: resources
Awesome Ocaml
A curated collection of awesome OCaml tools, frameworks, libraries and articles.
Stars: ✭ 2,177 (+1057.98%)
Mutual labels: resources
Accel Brain Code
The purpose of this repository is to make prototypes as case study in the context of proof of concept(PoC) and research and development(R&D) that I have written in my website. The main research topics are Auto-Encoders in relation to the representation learning, the statistical machine learning for energy-based models, adversarial generation networks(GANs), Deep Reinforcement Learning such as Deep Q-Networks, semi-supervised learning, and neural network language model for natural language processing.
Stars: ✭ 166 (-11.7%)
Mutual labels: semi-supervised-learning
Front End Performance Checklist
🎮 The only Front-End Performance Checklist that runs faster than the others
Stars: ✭ 13,815 (+7248.4%)
Mutual labels: resources
Awesome Deep Learning Music
List of articles related to deep learning applied to music
Stars: ✭ 2,195 (+1067.55%)
Mutual labels: resources
Front End Performance Checklist
🎮 더 빠르게 작동하는 프론트엔드 성능 체크리스트
Stars: ✭ 183 (-2.66%)
Mutual labels: resources
Ounotes
An Application built for students to access Notes , Question Papers , Syllabus and Resources for all Subjects of O.U (Osmania University) 📘👨🎓
Stars: ✭ 173 (-7.98%)
Mutual labels: resources
Cs Books
A list of textbooks for a Computer Science curriculum.
Stars: ✭ 175 (-6.91%)
Mutual labels: resources
Wq
📱🌐📋 wq: a modular framework supporting web / native geographic data collection apps for mobile surveys and citizen science. Powered by Django REST Framework, Redux, React, and Material UI.
Stars: ✭ 182 (-3.19%)
Mutual labels: survey
Stylealign
[ICCV 2019]Aggregation via Separation: Boosting Facial Landmark Detector with Semi-Supervised Style Transition
Stars: ✭ 172 (-8.51%)
Mutual labels: semi-supervised-learning
Googlecloudarchitectprofessional
Resources to prepare for Google Certified Cloud Architect Professional Exam - 2017
Stars: ✭ 177 (-5.85%)
Mutual labels: resources
Icopy
fclone telegram interface.Send commands to Telegram BOT for get a convience way to control fclone resources copy missions.
Stars: ✭ 188 (+0%)
Mutual labels: resources
Learn Anything
Organize world's knowledge, explore connections and curate learning paths
Stars: ✭ 13,532 (+7097.87%)
Mutual labels: resources
Awesome R Learning Resources
A curated collection of free resources to help deepen your understanding of the R programming language. Updated regularly. Contributions encouraged via pull request (see contributing.md).
Stars: ✭ 181 (-3.72%)
Mutual labels: resources
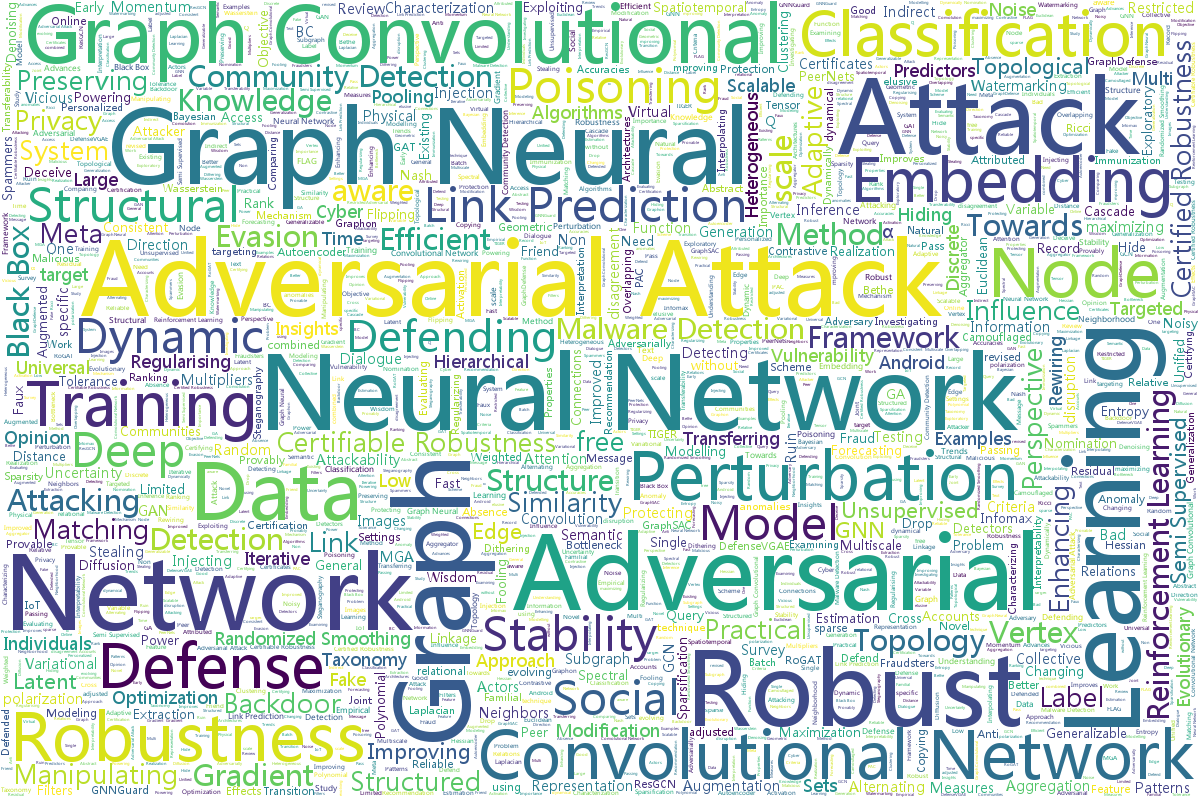
⚔🛡 Awesome Graph Adversarial Learning (Updating: 192 Papers)
- ⚔🛡 Awesome Graph Adversarial Learning (Updating: 192 Papers)
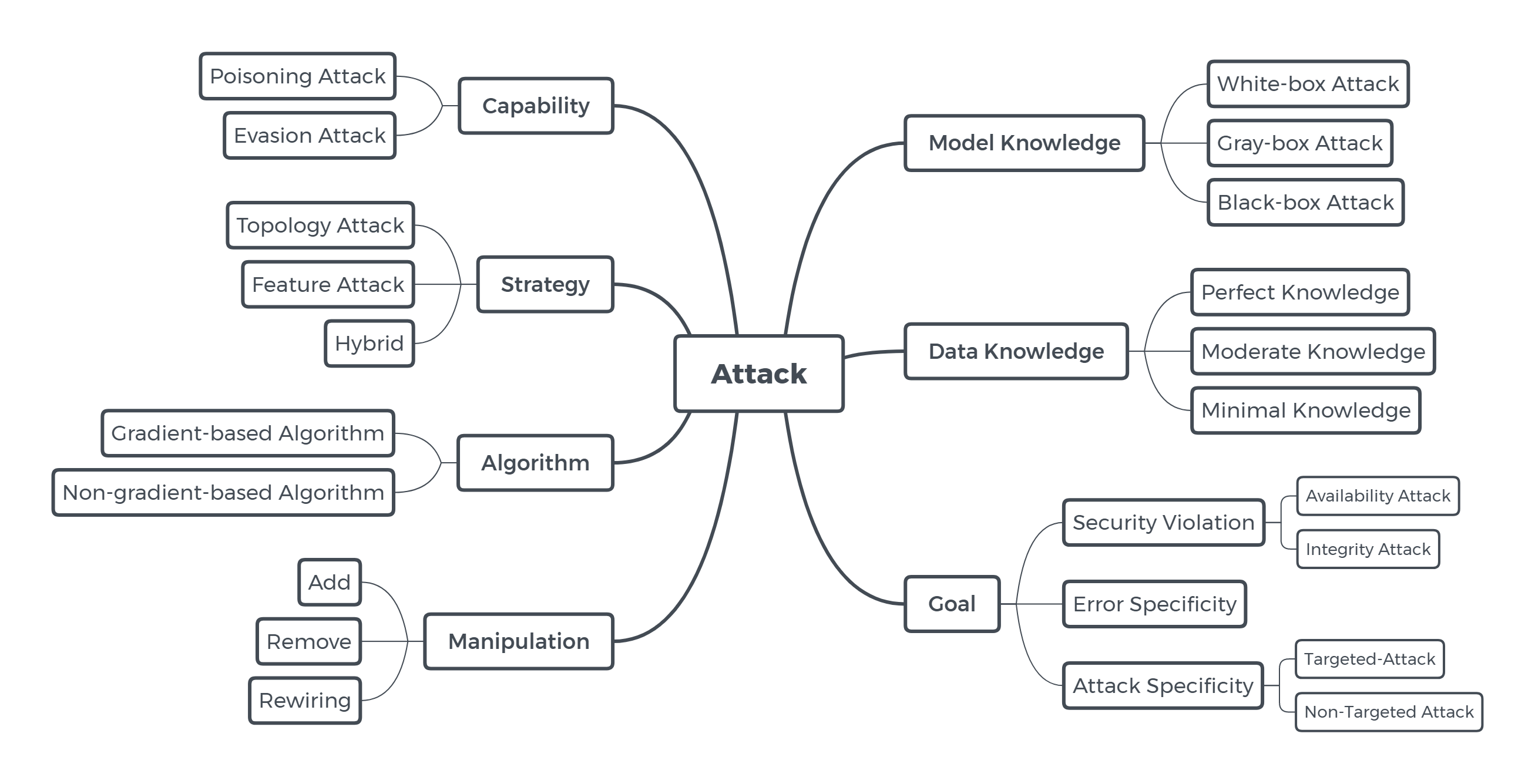
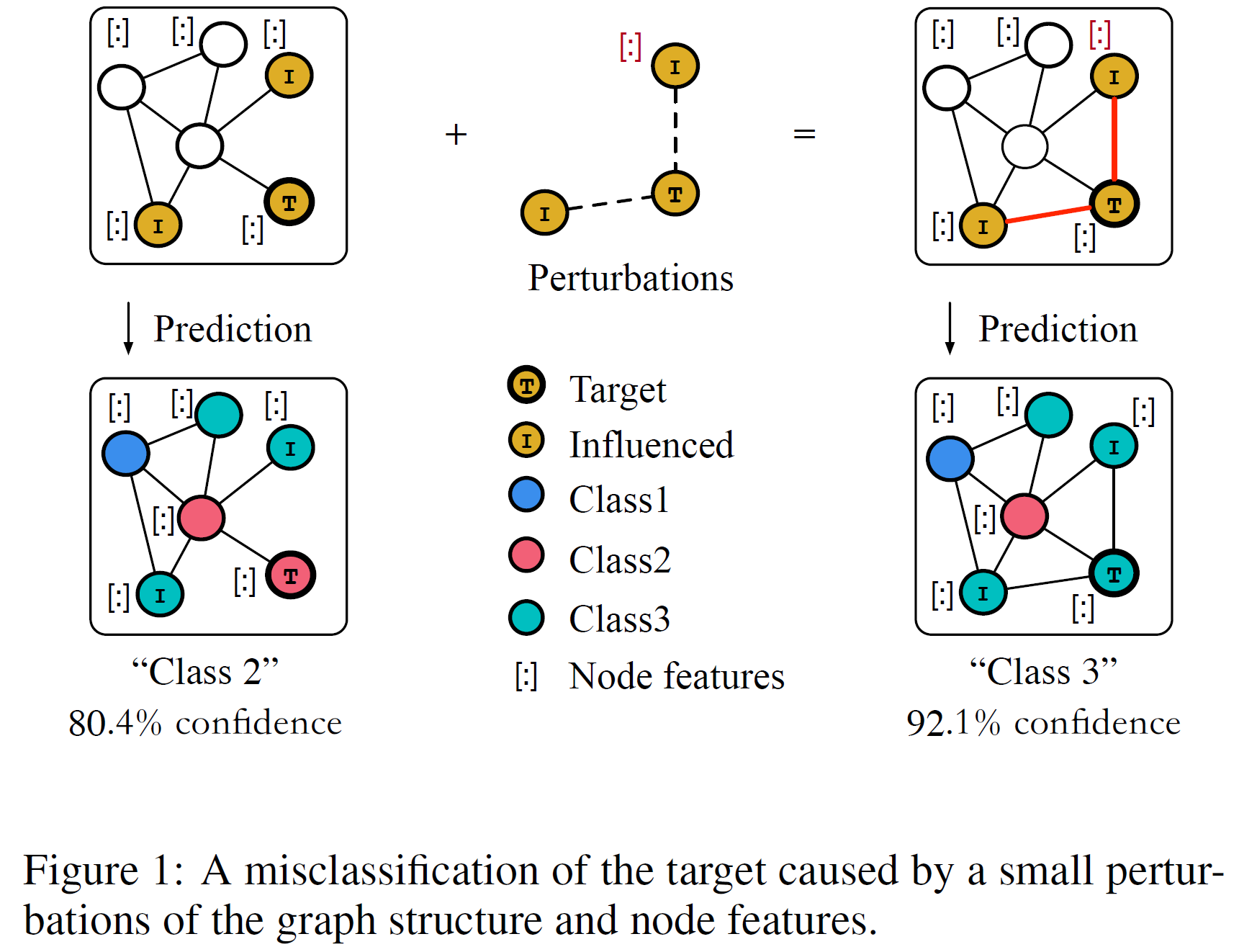
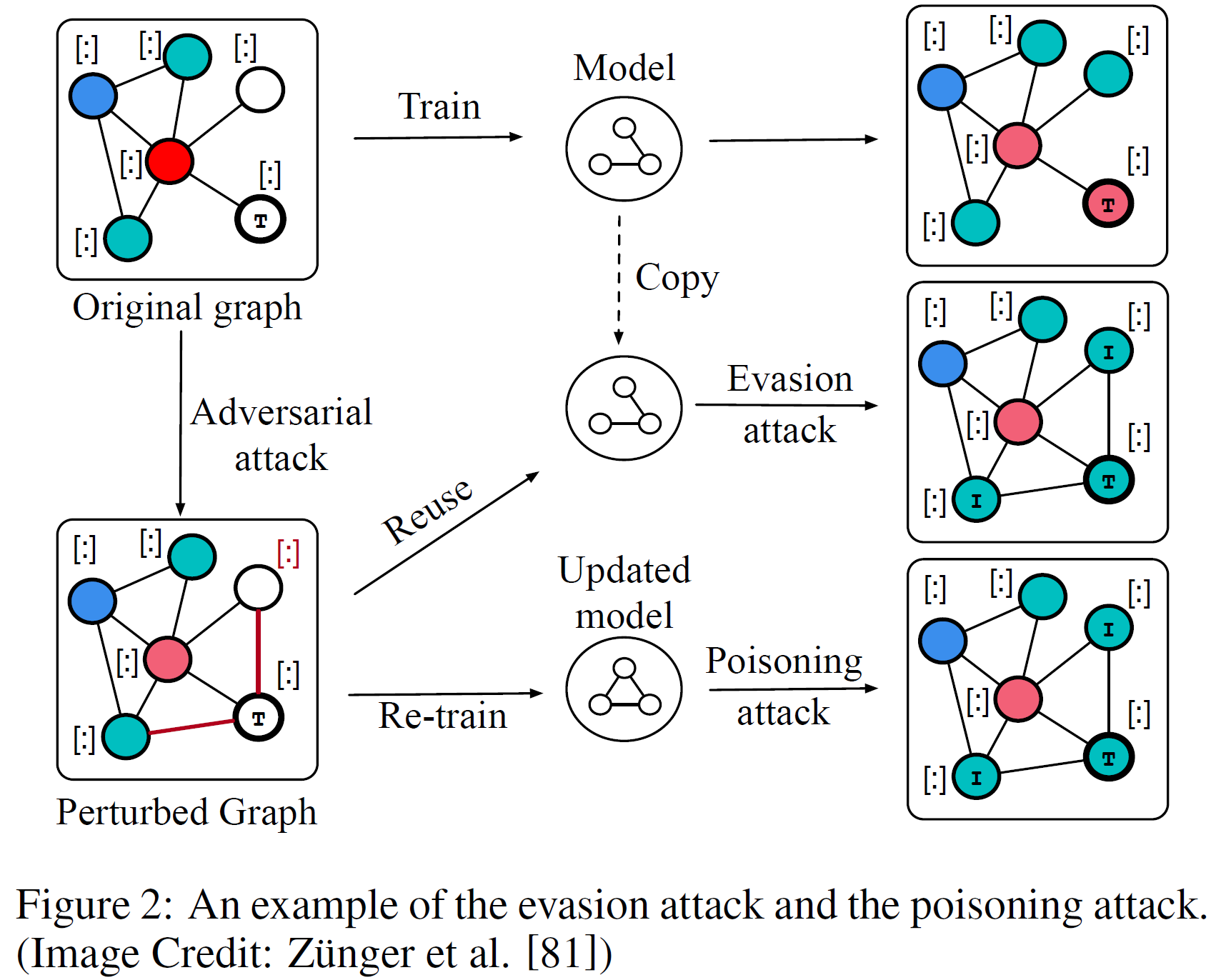
- ⚔ Attack
- Taxonomies of Attack
- 🛡 Defense
- 🔐 Robustness Certification
- ⚖ Stability
- 🚀 Others
- 📃 Survey
- 🔗 Resource
- ⚙ Toolbox
This repository contains Attack-related papers, Defense-related papers, Robustness Certification papers, etc., ranging from 2017 to 2021.
If you find this repo useful, please cite: A Survey of Adversarial Learning on Graph, Arxiv'20, Link
@article{chen2020survey,
title={A Survey of Adversarial Learning on Graph},
author={Chen, Liang and Li, Jintang and Peng, Jiaying and Xie,
Tao and Cao, Zengxu and Xu, Kun and He, Xiangnan and Zheng, Zibin},
journal={arXiv preprint arXiv:2003.05730},
year={2020}
}
⚔ Attack
2021
Stealing Links from Graph Neural Networks 📝USENIX Security
| Model | Link Stealing Attacks | Algorithm | Supervised/Unsupervised Training |
| Surrogate | GCN | Target Task | Link Prediction |
| Target Model | GCN | Baseline | Traditional Link Prediction Algorithms |
| Metric | AUC | Dataset | CiteSeer, Cora, Pubmed, AIDS, COX2, DHFR, ENZYMES, PROTEINS_full |
Membership Inference Attack on Graph Neural Networks 📝Arxiv
GraphAttacker: A General Multi-Task GraphAttack Framework 📝Arxiv
Graph Backdoor 📝USENIX Security
| Model | GTA | Algorithm | Gradient |
| Surrogate | Target Task | Node Classification, Graph Classification | |
| Target Model | GCN, GraphSAGE, GAT | Baseline | |
| Metric | ASR, AMC, BAD, ADD | Dataset | Fingerprint, Malware, AIDS, Toxicant, Bitcoin, Facebook |
Attacking Graph Neural Networks at Scale 📝AAAI workshop
Node-Level Membership Inference Attacks Against Graph Neural Networks 📝Arxiv
Reinforcement Learning For Data Poisoning on Graph Neural Networks 📝Arxiv
DeHiB: Deep Hidden Backdoor Attack on Semi-Supervised Learning via Adversarial Perturbation 📝AAAI
Graphfool: Targeted Label Adversarial Attack on Graph Embedding 📝Arxiv
2020
Adversarial Attack on Community Detection by Hiding Individuals 📝WWW Code
| Model | CD-ATTACK | Algorithm | Graph generation |
| Surrogate | GCN | Target Task | Community Detection |
| Target Model | GCN, Node2vec + K-means, ComE | Baseline | DICE, MBA, RTA |
| Metric | Hiding performance measure M1 & M2 | Dataset | DBLP, Finance |
Manipulating Node Similarity Measures in Networks 📝AAMAS
| Model | FPTA | Algorithm | |
| Surrogate | Target Task | Node Similarity | |
| Target Model | Node Similarity Measures | Baseline | Random, Greedy, High Jaccard Similarity (HJ) |
| Metric | Time | Dataset | Barabasi-Albert (BA), Erdos-Renyi (ER) |
A Restricted Black-box Adversarial Framework Towards Attacking Graph Embedding Models 📝AAAI Code
Indirect Adversarial Attacks via Poisoning Neighbors for Graph Convolutional Networks 📝BigData
| Model | POISONPROBE | Algorithm | Binary search |
| Surrogate | GCN | Target Task | Node Classification |
| Target Model | GCN | Baseline | Nettack |
| Metric | ASR, Recall | Dataset | CiteSeer, Cora-ML |
Non-target-specific Node Injection Attacks on Graph Neural Networks: A Hierarchical Reinforcement Learning Approach 📝WWW
| Model | NIPA | Algorithm | Reinforcement learning, Nodes injection |
| Surrogate | GCN | Target Task | Node Classification |
| Target Model | GCN | Baseline | Random, FGA, Preferential attack |
| Metric | Accuracy | Dataset | Cora-ML, CiteSeer, Pubmed |
Adversarial Attacks on Graph Neural Networks: Perturbations and their Patterns 📝TKDD
| Model | Fasttack | Algorithm | Perturbations Impact Ranking |
| Surrogate | GCN | Target Task | Node Classification |
| Target Model | GCN, CLN, DeepWalk | Baseline | Random, FGSM |
| Metric | Classification Margin, Accuracy | Dataset | Cora-ML, CiteSeer, Polblogs, Pubmed |
An Efficient Adversarial Attack on Graph Structured Data 📝IJCAI Workshop
| Model | Algorithm | ||
| Surrogate | Target Task | ||
| Target Model | Baseline | ||
| Metric | Dataset |
Practical Adversarial Attacks on Graph Neural Networks 📝ICML Workshop
| Model | GC-RWCS | Algorithm | Greedy |
| Surrogate | Target Task | Node Classification | |
| Target Model | GCN, JKNetConcat, JKNetMaxpool | Baseline | Random, Degree, Betweenness, PageRank |
| Metric | Accuracy | Dataset | Cora, CiteSeer, Pubmed |
Link Prediction Adversarial Attack Via Iterative Gradient Attack 📝IEEE Trans
| Model | IGA | Algorithm | Gradient |
| Surrogate | GAE | Target Task | Link Prediction |
| Target Model | GAE, LRW, DeepWalk, Node2vec, CN, RA, Katz | Baseline | RAN, DICE, GA |
| Metric | ASR, AML | Dataset | NS, Yeast, FaceBook |
Adversarial Attacks on Link Prediction Algorithms Based on Graph Neural Networks 📝Asia CCS
| Model | GGSP, OGSP | Algorithm | Greedy |
| Surrogate | Target Task | Link Prediction | |
| Target Model | SEAL | Baseline | |
| Metric | ASR, AUC | Dataset | Cora-ML, CiteSeer, Pubmed |
Adversarial attack on BC classification for scale-free networks 📝AIP Chaos
| Model | DALR, DILR | Algorithm | Degree |
| Surrogate | Target Task | Network Structure | |
| Target Model | Broido and Clauset Classification | Baseline | RLR |
| Metric | Accuracy | Dataset | Networks generated by BA and UCM |
Attackability Characterization of Adversarial Evasion Attack on Discrete Data 📝KDD
| Model | OMPGS | Algorithm | Gradient Guided Greedy Search |
| Surrogate | Target Task | Classification on Sequential Discret Data | |
| Target Model | LSTM, LSTM-Sub, LSTM-Noise | Baseline | SGS, FSGS, GradAttack, OMPGS-Rand |
| Metric | ANC, AI, SR (Attack Performance) | Dataset | IPS, HER |
MGA: Momentum Gradient Attack on Network 📝Arxiv
| Model | MGA | Algorithm | Momentum gradient |
| Surrogate | GCN | Target Task | Node Classification, Community Detection |
| Target Model | GCN, DeepWalk, Node2vec, GraphGAN, LPA, Louvain | Baseline | GradArgmax, RL-S2V, Nettack, FGA |
| Metric | ASR, AML | Dataset | Cora, CiteSeer, Polblogs |
Adversarial Attacks to Scale-Free Networks: Testing the Robustness of Physical Criteria 📝Arxiv
| Model | RLR, DALR, DILR | Algorithm | Random, Degree |
| Surrogate | Target Task | Network Structure | |
| Target Model | Physical Criteria | Baseline | |
| Metric | AML, (diagonal) distance, clustering coefficient | Dataset | Generated simplex networks |
Graph Universal Adversarial Attacks: A Few Bad Actors Ruin Graph Learning Models 📝Arxiv Code
| Model | GUA | Algorithm | Gradient |
| Surrogate | GCN | Target Task | Node Classification |
| Target Model | GCN, DeepWalk, Node2Vec, GAT | Baseline | Random, VCA, FGA |
| Metric | ASR, AML | Dataset | Cora, CiteSeer, Polblogs |
Adversarial Perturbations of Opinion Dynamics in Networks 📝Arxiv
| Model | Algorithm | Graph Laplacian | |
| Surrogate | Friedkin-Johnsen model | Target Task | Network Disruption |
| Target Model | Baseline | Opinion dynamics model | |
| Metric | Dataset |
Network disruption: maximizing disagreement and polarization in social networks 📝Arxiv Code
| Model | Greedy et al. | Algorithm | Greedy algorithm et al. |
| Surrogate | Friedkin-Johnsen model | Target Task | Network Disruption |
| Target Model | Friedkin-Johnsen model | Baseline | |
| Metric | Disagreement, Polarization |
Dataset | Synthetic networks, Reddit, Twitter |
Scalable Attack on Graph Data by Injecting Vicious Nodes 📝ECML-PKDD
| Model | AFGSM | Algorithm | Gradient |
| Surrogate | GCN | Target Task | Node Classification |
| Target Model | GCN, GAT, DeepWalk | Baseline | Nettack, FGSM, Metattack |
| Metric | Accuracy | Dataset | CiteSeer, Cora, DBLP, Pubmed, Reddit |
Adversarial Attack on Hierarchical Graph Pooling Neural Networks|Gradient-Based Pooling Attack 📝Arxiv
| Model | Gradient-Based Pooling Attack | Algorithm | Gradient |
| Surrogate | 1-Layer HGP | Target Task | Graph Classification |
| Target Model | HGP, SAG, HGP-SL | Baseline | Random |
| Metric | Accuracy | Dataset | DD, Mutagenicity, ER_MD, DHFR, AIDS, BZR |
Backdoor Attacks to Graph Neural Networks 📝ICLR OpenReview
| Model | Subgraph-based Backdoor Attacks | Algorithm | Subgraph Generation |
| Surrogate | Target Task | Graph Classification | |
| Target Model | GIN | Baseline | Clean |
| Metric | Accuracy, ASR | Dataset | Bitcoin, Twitter, COLLAB |
Adversarial Attack on Large Scale Graph 📝Arxiv Code
| Model | SGA | Algorithm | Gradient |
| Surrogate | SGC | Target Task | Node Classification |
| Target Model | GCN, SGC, GAT, ClusterGCN, GraphSAGE | Baseline | GradArgmax, Nettack |
| Metric | DAC, Accuracy, Classification Margin | Dataset | Cora, CiteSeer, Pubmed, Reddit |
Efficient Evasion Attacks to Graph Neural Networks via Influence Function 📝Arxiv
| Model | Influence-based Attack | Algorithm | Influence Function |
| Surrogate | Target Task | Node Classification | |
| Target Model | GCN, SGC | Baseline | OTA-KL, OTA-UL, Iter-KL, Iter-UL |
| Metric | ASR, Running Time | Dataset | Cora, CiteSeer, Pubmed |
Reinforcement Learning-based Black-Box Evasion Attacks to Link Prediction in Dynamic Graphs 📝Arxiv
| Model | RL-based Attack | Algorithm | Reinforcement Learning |
| Surrogate | Target Task | Link Prediction | |
| Target Model | DyGCN | Baseline | Random-whole, Random-partial |
| Metric | F1 | Dataset | Haggle, Hypertext, Trapping |
Semantic-preserving Reinforcement Learning Attack Against Graph Neural Networks for Malware Detection 📝Arxiv
Adaptive Adversarial Attack on Graph Embedding via GAN 📝SocialSec
Scalable Adversarial Attack on Graph Neural Networks with Alternating Direction Method of Multipliers 📝Arxiv
One Vertex Attack on Graph Neural Networks-based Spatiotemporal Forecasting 📝ICLR OpenReview
Single-Node Attack for Fooling Graph Neural Networks 📝ICLR OpenReview
Black-Box Adversarial Attacks on Graph Neural Networks as An Influence Maximization Problem 📝ICLR OpenReview
Adversarial Attacks on Deep Graph Matching 📝NeurIPS
Black-Box Adversarial Attacks on Graph Neural Networks with Limited Node Access 📝NeurIPS
A Graph Matching Attack on Privacy-Preserving Record Linkage 📝CIKM
Cross Entropy Attack on Deep Graph Infomax 📝IEEE ISCAS
Model Extraction Attacks on Graph Neural Networks: Taxonomy and Realization 📝Arxiv
Learning to Deceive Knowledge Graph Augmented Models via Targeted Perturbation 📝ICLR OpenReview Code
Adversarial Label-Flipping Attack and Defense for Graph Neural Networks 📝ICDM
Exploratory Adversarial Attacks on Graph Neural Networks 📝ICDM Code
Attacking Graph-Based Classification without Changing Existing Connections 📝ACSAC
Query-free Black-box Adversarial Attacks on Graphs 📝Arxiv
2019
A Unified Framework for Data Poisoning Attack to Graph-based Semi-supervised Learning 📝NeurIPS Code
| Model | G-SSL | Algorithm | Gradient based asymptotic linear algorithm |
| Surrogate | Target Task | Classification, Regression | |
| Target Model | Label propagation & regularization algs | Baseline | Random, PageRank, Degree |
| Metric | Error rate, RMSE | Dataset | cadata, E2006, mnist17, rcv1 |
Adversarial Examples on Graph Data: Deep Insights into Attack and Defense 📝IJCAI Code
| Model | IG-FGSM, IG-JSMA | Algorithm | Gradient |
| Surrogate | GCN | Target Task | Node Classification |
| Target Model | GCN | Baseline | FGSM, JSMA, Nettack |
| Metric | Classification Margin, Accuracy | Dataset | Cora, CiteSeer, PolBlogs |
Topology Attack and Defense for Graph Neural Networks: An Optimization Perspective 📝IJCAI Code
| Model | PGD, Min-Max | Algorithm | Gradient |
| Surrogate | GCN | Target Task | Node Classification |
| Target Model | GCN | Baseline | DICE, Metattack, Greedy |
| Metric | Misclassification Rate | Dataset | Cora, CiteSeer |
Adversarial Attacks on Graph Neural Networks via Meta Learning 📝ICLR Code
| Model | Metattack | Algorithm | Gradient |
| Surrogate | GCN | Target Task | Node Classification |
| Target Model | GCN, CLN, DeepWalk | Baseline | DICE, Nettack, First-order |
| Metric | Misclassification Rate, Accuracy | Dataset | Cora, CiteSeer, PolBlogs, PubMed |
αCyber: Enhancing Robustness of Android Malware Detection System against Adversarial Attacks on Heterogeneous Graph based Model 📝CIKM
| Model | HG-Attack | Algorithm | Label propagation algorithm, Nodes injection |
| Surrogate | Target Task | Malware Detection | |
| Target Model | Orig-HGC | Baseline | AN-Attack |
| Metric | TP, TN, FP, FN, F1, Precision, Recall, Accuracy | Dataset | Tencent Security Lab Dataset |
Data Poisoning Attack against Knowledge Graph Embedding 📝IJCAI
| Model | Algorithm | Knowledge embedding | |
| Surrogate | Target Task | Fact Plausibility Prediction | |
| Target Model | TransE, TransR, RESCAL | Baseline | RA |
| Metric | MRR, [email protected] | Dataset | FB15k, WN18 |
GA Based Q-Attack on Community Detection 📝TCSS
| Model | Q-Attack | Algorithm | Genetic algorithm |
| Surrogate | Target Task | Community Detection | |
| Target Model | FN, Lou, SOA, LPA, INF, Node2vec+KM | Baseline | Random, CDA, DBA |
| Metric | Modularity Q, NMI | Dataset | Karate, Dolphins, Football, Polbooks |
Attacking Graph-based Classification via Manipulating the Graph Structure 📝CCS
| Model | Algorithm | ||
| Surrogate | LinLBP | Target Task | Node Classification, Evasion |
| Target Model | LinLBP, JWP, LBP, RW, LINE, DeepWalk, Node2vec, GCN | Baseline | Random, Nettack |
| Metric | FNR, FPR | Dataset | Facebook, Enron, Epinions, Twitter, Google+ |
Adversarial Attacks on Node Embeddings via Graph Poisoning 📝ICML Code
Network Structural Vulnerability A Multi-Objective Attacker Perspective 📝IEEE Trans
Multiscale Evolutionary Perturbation Attack on Community Detection 📝Arxiv
| Model | EPA | Algorithm | Genetic algorithm |
| Surrogate | Target Task | Community Detection | |
| Target Model | GRE, INF, LOU | Baseline |
|
| Metric | NMI, ARI | Dataset | Synthetic networks, Football, Email, Polblogs |
Time-aware Gradient Attack on Dynamic Network Link Prediction 📝IJCAI
| Model | TGA-Tra, TGA-Gre | Algorithm | Gradient |
| Surrogate | DDNE | Target Task | Link Prediction |
| Target Model | DDNE, ctRBM, GTRBM, dynAERNN | Baseline | Random, DGA, CNA |
| Metric | ASR, AML | Dataset | RADOSLAW, LKML, FB-WOSN |
Attacking Graph Convolutional Networks via Rewiring 📝Arxiv
| Model | ReWatt | Algorithm | Reinforcement Learning |
| Surrogate | GCN | Target Task | Graph Classification |
| Target Model | GCN | Baseline | RL-S2V, RA |
| Metric | ASR | Dataset | REDDIT-MULTI-12K, REDDIT-MULTI-5K, IMDB-MULTI |
Unsupervised Euclidean Distance Attack on Network Embedding 📝Arxiv
| Model | EDA | Algorithm | Genetic algorithm |
| Surrogate | DeepWalk | Target Task | Node Classification, Community Detection |
| Target Model | HOPE, LPA, EM, DeepWalk | Baseline | Random, DICE, RLS, DBA |
| Metric | NMI, Micro-F1, Macro-F1 | Dataset | Karate, Game, Dolphin |
Generalizable Adversarial Attacks with Latent Variable Perturbation Modelling 📝Arxiv
| Model | DAGAER | Algorithm | Generative model |
| Surrogate | VGAE | Target Task | Node Classification |
| Target Model | GCN | Baseline | Nettack |
| Metric | ASR | Dataset | Cora, CiteSeer |
Vertex Nomination, Consistent Estimation, and Adversarial Modification 📝Arxiv
PeerNets Exploiting Peer Wisdom Against Adversarial Attacks 📝ICLR (Poster) Code
2018
Adversarial Attack on Graph Structured Data 📝ICML Code
| Model | RL-S2V, GradArgmax, GeneticAlg | Algorithm | Reinforcement learning, Gradient, Genetic algorithm |
| Surrogate | GCN | Target Task | Node Classification, Graph Classification |
| Target Model | GCN, GNN | Baseline | Random |
| Metric | Accuracy | Dataset | Cora, CiteSeer, PolBlogs, Finance |
Adversarial Attacks on Neural Networks for Graph Data 📝KDD Code
| Model | Nettack | Algorithm | Greedy search & gradient |
| Surrogate | GCN | Target Task | Node Classification |
| Target Model | GCN, CLN, DeepWalk | Baseline | Rnd, FGSM |
| Metric | Classification Margin, Accuracy | Dataset | Cora-ML, CiteSeer, PolBlogs |
Attacking Similarity-Based Link Prediction in Social Networks 📝AAMAS
| Model | Approx-Local | Algorithm | Similarity methods |
| Surrogate | Target Task | Link Prediction | |
| Target Model | Local & Global similarity metrics | Baseline | Random, GreedyBase |
| Metric | Katz Similarity, ACT Distance, Similarity Score | Dataset | Random network, Facebook |
Hiding Individuals and Communities in a Social Network 📝Nature Human Behavior
| Model | DICE | Algorithm | Disconnect Internally, Connect Externally |
| Surrogate | Target Task | ||
| Target Model | Baseline | ||
| Metric | Dataset |
Fake Node Attacks on Graph Convolutional Networks 📝Arxiv
| Model | Greedy, Greedy GAN | Algorithm | Gradient |
| Surrogate | GCN, GAN | Target Task | Node Classification |
| Target Model | GCN | Baseline | RA |
| Metric | Accuracy, F1 Score, ASR | Dataset | Cora, CiteSeer |
Attack Tolerance of Link Prediction Algorithms: How to Hide Your Relations in a Social Network 📝Arxiv
| Model | CTR OTC | Algorithm | Neighbour score based on graph structure |
| Surrogate | Target Task | Link Prediction | |
| Target Model | Traditional Link Prediction Algs | Baseline | |
| Metric | AUC, AP | Dataset | WTC 9/11, ScaleFree, Facebook, Random network |
Fast Gradient Attack on Network Embedding 📝Arxiv
| Model | FGA | Algorithm | Gradient |
| Surrogate | GCN | Target Task | Node Classification, Community Detection |
| Target Model | GCN, GraRep, DeepWalk, Node2vec, LINE, GraphGAN | Baseline | Random, DICE, Nettack |
| Metric | ASR, AML | Dataset | Cora, CiteSeer, PolBlogs |
Data Poisoning Attack against Unsupervised Node Embedding Methods 📝Arxiv
| Model | Opt-attack | Algorithm | Gradient |
| Surrogate | DeepWalk, LINE | Target Task | Link Prediction |
| Target Model | DeepWalk, LINE, Node2vec, SC, GAE | Baseline | Random, PageRank, Degree sum, Shortest path |
| Metric | Similarity Score, AP | Dataset | Cora, CiteSeer, Facebook |
2017
Practical Attacks Against Graph-based Clustering 📝CCS
| Model | Targeted noise injection, Small community attack | Algorithm | Noise Injection |
| Surrogate | Target Task | Graph Clustering, Community Detection | |
| Target Model | SVD, Node2vec, Community Detection Algs | Baseline | |
| Metric | ASR, FPR | Dataset | Reverse Engineered DGA Domains, NXDOMAIN |
Taxonomies of Attack
|
|
🛡 Defense
2021
UAG: Uncertainty-Aware Attention Graph Neural Network for Defending Adversarial Attacks 📝AAAI
Uncertainty-Matching Graph Neural Networks to Defend Against Poisoning Attacks 📝AAAI
Randomized Generation of Adversary-Aware Fake Knowledge Graphs to Combat Intellectual Property Theft 📝AAAI
Power up! Robust Graph Convolutional Network against Evasion Attacks based on Graph Powering 📝AAAI Code
| Model | r-GCN, VPN | Algorithm | Graph Powering |
| Defense Type | Objective Based | Target Task | Node Classification |
| Target Model | GCN | Baseline | ManiReg, SemiEmb, LP, DeepWalk, ICA, Planetoid, GCN |
| Metric | Accuracy, Robustness Merit, Attack Deterioration | Dataset | CiteSeer, Cora, Pubmed |
Personalized privacy protection in social networks through adversarial modeling 📝AAAI
Interpretable Stability Bounds for Spectral Graph Filters 📝Arxiv
Towards Robust Graph Contrastive Learning 📝Arxiv
2020
Transferring Robustness for Graph Neural Network Against Poisoning Attacks 📝WSDM Code
| Model | PA-GNN | Algorithm | Penalized Aggregation, Meta Learning |
| Defense Type | Structure Based | Target Task | Node Classification |
| Target Model | GNN | Baseline | GCN, GAT, GCN-Jaccard, RGCN, VPN |
| Metric | Accuracy | Dataset | Pubmed, Reddit, Yelp |
All You Need Is Low (Rank): Defending Against Adversarial Attacks on Graphs 📝WSDM Code
| Model | GCN-SVD | Algorithm | SVD |
| Defense Type | Preprocessing | Target Task | Node Classification |
| Target Model | GCN | Baseline | GCN |
| Metric | Accuracy, Classification Margin | Dataset | CiteSeer, Cora-ML, PolBlogs |
How Robust Are Graph Neural Networks to Structural Noise? 📝DLGMA
| Model | Algorithm | Adversarial Training | |
| Defense Type | Adversarial Training | Target Task | Node Classification |
| Target Model | GIN | Baseline | GIN |
| Metric | F1 score | Dataset | Constructed graph |
Robust Detection of Adaptive Spammers by Nash Reinforcement Learning 📝KDD Code
| Model | Nash-Detect | Algorithm | A minimax game |
| Defense Type | Detection Based | Target Task | Spam Detection |
| Target Model | Baseline | Spam Detector | |
| Metric | Practical Effect, Accuracy | Dataset | YelpChi, YelpNYC, YelpZip |
Graph Structure Learning for Robust Graph Neural Networks 📝KDD Code
| Model | Pro-GNN | Algorithm | Learns the graph structure and the GNN parameters simultaneously |
| Defense Type | Hybrid | Target Task | Node Classification |
| Target Model | GCN | Baseline | GAT, GCN-Jaccard, GCN-SVD |
| Metric | Accuracy | Dataset | Cora, CiteSeer, Polblogs, Pubmed |
Robust Graph Representation Learning via Neural Sparsification 📝ICML
| Model | NeuralSparse | Algorithm | Subgraphs Sampling |
| Defense Type | Preprocessing-based | Target Task | Node Classification |
| Target Model | GCN, GraphSAGE, GAT, GIN | Baseline | SS/RD, DropEdge, LDS |
| Metric | Micro-F1,AUC, Accuracy | Dataset | Reddit, PPI, Transaction, Cora, CiteSeer |
On The Stability of Polynomial Spectral Graph Filters 📝ICASSP Code
| Model | Algorithm | Polynomial graph filters | |
| Defense Type | Structure Based | Target Task | Graph signal processing |
| Target Model | GNN | Baseline | |
| Metric | Laplacian distance | Dataset | Barabási-Albert, Sensor network |
Transferring Robustness for Graph Neural Network Against Poisoning Attacks 📝WSDM Code
| Model | PA-GNN | Algorithm | Penalized Aggregation, Meta Learning |
| Defense Type | Structure Based | Target Task | Node Classification |
| Target Model | GNN | Baseline | GCN, GAT, GCN-Jaccard, RGCN, VPN |
| Metric | Accuracy | Dataset | Pubmed, Reddit, Yelp |
On the Robustness of Cascade Diffusion under Node Attacks 📝WWW Code
| Model | Algorithm | SEMR | |
| Defense Type | Target Task | Cascade Diffusion | |
| Target Model | IC Model | Baseline | NetShield |
| Metric | EMR, RNI, RIM | Dataset | Blogs, Minnesota, VK, Advogato, DBLP, BrightKite, ... |
Friend or Faux: Graph-Based Early Detection of Fake Accounts on Social Networks 📝WWW
| Model | Algorithm | SybilEdge | |
| Defense Type | Preprocessing-based | Target Task | Fake Detection |
| Target Model | Graph-based models | Baseline | SybilRank, SybilBelief, SybilSCAR |
| Metric | AUC, RejectRate, SybilEdgeTR | Dataset | Facebook network |
Towards an Efficient and General Framework of Robust Training for Graph Neural Networks 📝ICASSP
| Model | GTA, ZO-GTA | Algorithm | Greedy search, Zeroth-order |
| Defense Type | Adversarial-based | Target Task | Node Classification |
| Target Model | GNN | Baseline | DICE, CE-PGD, CW-PGD |
| Metric | Misclassification rate | Dataset | Cora, CiteSeer, PubMed |
Robust Graph Learning From Noisy Data 📝IEEE Trans
| Model | RGC | Algorithm | Graph regularization |
| Defense Type | Prepocessing-based | Target Task | Clustering, Semisupervised Classification |
| Target Model | RPCA | Baseline | SC, RKKM, RSC, SSR, CAN, TLSC |
| Metric | Accuracy, NMI, Purity | Dataset | YALE, JAFFE, ORL, TR41, TR45, ... |
Robust Training of Graph Convolutional Networks via Latent Perturbation 📝ECML-PKDD Code
| Model | LAT-GCN | Algorithm | Perturbing latent representations |
| Defense Type | Structure Based | Target Task | Node Classification, Link prediction, Recommendation |
| Target Model | GCN | Baseline | GCN, ADV-GCN, MIN-MAX GCN, ... |
| Metric | CPU time, Accuracy, AUC, AP | Dataset | CiteSeer, Cora, PubMed, MovieLens 100k |
Enhancing Graph Neural Network-based Fraud Detectors against Camouflaged Fraudsters 📝CIKM Code
| Model | CARE-GNN | Algorithm | Reinforcement Learning |
| Defense Type | Hybrid | Target Task | |
| Target Model | GCN, GAT, RGCN, GraphSAGE | Baseline | GeniePath, Player2Vec, SemiGNN, GraphConsis |
| Metric | AUC, Recall | Dataset | Yelp, Amazon |
Provably Robust Node Classification via Low-Pass Message Passing 📝ICDM
Dynamic Knowledge Graph-based Dialogue Generation with Improved Adversarial Meta-Learning 📝Arxiv
| Model | KDAD | Algorithm | Adversarial Meta-learning |
| Defense Type | Objective-based | Target Task | Dialogue Generation |
| Target Model | Qadpt | Baseline | TAware, Qadpt |
| Metric | BLEU, PPL, DISTINCT, ... | Dataset | HGZHZ |
Robust Collective Classification against Structural Attacks 📝Preprint
| Model | R-AMN | Algorithm | Bound Analysis |
| Defense Type | Objective-based | Target Task | Node Classification |
| Target Model | AMN | Baseline | Struct-RSAD |
| Metric | Accuracy | Dataset | Reuters, WebKB, Cora, CiteSeer |
Tensor Graph Convolutional Networks for Multi-relational and Robust Learning 📝Arxiv
| Model | TGCN | Algorithm | Edge-dithering |
| Defense Type | Processing-based | Target Task | Node Classification, Protein Prediction |
| Target Model | GCN | Baseline | GCN |
| Metric | Accuracy, Macro F1 | Dataset | Cora, CiteSeer, Pubmed, Polblogs, ... |
Topological Effects on Attacks Against Vertex Classification 📝Arxiv
| Model | StratDegree, GreedyCover | Algorithm | GreedyCover |
| Defense Type | Processing-based | Target Task | Node Classification |
| Target Model | GCN | Baseline | Random Selection |
| Metric | Required budget, Median margin | Dataset | Cora, CiteSeer, Pubmed, Polblogs |
Evaluating Graph Vulnerability and Robustness using TIGER 📝Arxiv
| Model | TIGER | Algorithm | |
| Defense Type | Hybrid | Target Task | Node Classification |
| Target Model | Baseline | ||
| Metric | Average vertex betweenness, Spectral scaling, Effective resistance | Dataset | US power grid, Water Distribution Network |
Adversarial Perturbations of Opinion Dynamics in Networks 📝Arxiv
| Model | Algorithm | ||
| Defense Type | Target Task | Network Disruption | |
| Target Model | Opinion dynamics models | Baseline | |
| Metric | Polarization-disagreement index | Dataset |
DefenseVGAE: Defending against Adversarial Attacks on Graph Data via a Variational Graph Autoencoder 📝Arxiv Code
| Model | DefenceVGAE | Algorithm | VGAE |
| Defense Type | Processing-based | Target Task | Node Classification |
| Target Model | GCN | Baseline | GCN-Jaccard, GCN-SVD, RGCN |
| Metric | Accuracy | Dataset | Cora, CiteSeer, PolBlogs |
GNNGuard: Defending Graph Neural Networks against Adversarial Attacks 📝NeurIPS Code
| Model | GNNGuard | Algorithm | Network theory of homophily |
| Defense Type | Structure-based | Target Task | Node Classification |
| Target Model | GCN, GAT, GIN, ... | Baseline | GNN-Jaccard, RobustGCN, GNN-SVD |
| Metric | Accuracy | Dataset | Cora, CiteSeer, ogbn-arxiv, DP |
Adversarial Privacy Preserving Graph Embedding against Inference Attack 📝Arxiv Code
| Model | APDGE | Algorithm | Adversarial Privacy-Purged |
| Defense Type | Structure-based | Target Task | Privacy Protection |
| Target Model | GAE | Baseline | GAE RM, CDSPIA |
| Metric | Macro F1 | Dataset | Yale, Rochester |
RoGAT: a robust GNN combined revised GAT with adjusted graphs 📝Arxiv
ResGCN: Attention-based Deep Residual Modeling for Anomaly Detection on Attributed Networks 📝Arxiv
A Novel Defending Scheme for Graph-Based Classification Against Graph Structure Manipulating Attack 📝SocialSec
Iterative Deep Graph Learning for Graph Neural Networks: Better and Robust Node Embeddings 📝NeurIPS Code
Towards Robust Graph Neural Networks against Label Noise 📝ICLR OpenReview
Graph Adversarial Networks: Protecting Information against Adversarial Attacks 📝ICLR OpenReview Code
Ricci-GNN: Defending Against Structural Attacks Through a Geometric Approach 📝ICLR OpenReview
Variational Inference for Graph Convolutional Networks in the Absence of Graph Data and Adversarial Settings 📝NeurIPS Code
Provable Overlapping Community Detection in Weighted Graphs 📝NeurIPS
Community detection in sparse time-evolving graphs with a dynamical Bethe-Hessian 📝NeurIPS
Node Copying for Protection Against Graph Neural Network Topology Attacks 📝Arxiv
Anti-perturbation of Online Social Networks by Graph Label Transition 📝Arxiv
Adversarial Detection on Graph Structured Data 📝PPMLP
Learning Graph Embedding with Adversarial Training Methods 📝IEEE Transactions on Cybernetics
Unsupervised Adversarially-Robust Representation Learning on Graphs 📝Arxiv
I-GCN: Robust Graph Convolutional Network via Influence Mechanism 📝Arxiv
Adversary for Social Good: Protecting Familial Privacy through Joint Adversarial Attacks 📝AAAI
Smoothing Adversarial Training for GNN 📝IEEE TCSS
Graph Structure Reshaping Against Adversarial Attacks on Graph Neural Networks 📝NIPS under review Code
2019
Topology Attack and Defense for Graph Neural Networks: An Optimization Perspective 📝IJCAI Code
| Model | Algorithm | Adversarial Training | |
| Defense Type | Adversarial Training | Target Task | Node Classification |
| Target Model | GCN | Baseline | GCN |
| Metric | Misclassification Rate, Accuracy | Dataset | Cora, CiteSeer |
Adversarial Examples on Graph Data: Deep Insights into Attack and Defense 📝IJCAI Code
| Model | GCN-Jaccard | Algorithm | Drop Edges |
| Defense Type | Preprocessing | Target Task | Node Classification |
| Target Model | GCN | Baseline | GCN |
| Metric | Classification Margin, Accuracy | Dataset | Cora-ML, CiteSeer, PolBlogs |
Investigating Robustness and Interpretability of Link Prediction via Adversarial Modifications 📝NAACL Code
| Model | CRIAGE | Algorithm | Adversarial Modification |
| Defense Type | Robustness Evaluation | Target Task | Link Prediction |
| Target Model | Knowledge Graph Embedding | Baseline | |
| Metric | [email protected], MRR | Dataset | Nations, Kinship, WN18, YAGO3-10 |
Robust Graph Convolutional Networks Against Adversarial Attacks 📝KDD Code
| Model | RGCN | Algorithm | Gaussian-based Graph Convolution and Attention Mechanism |
| Defense Type | Structure Based | Target Task | Node Classification |
| Target Model | GCN | Baseline | GCN, GAT |
| Metric | Accuracy | Dataset | Cora, CiteSeer, Pubmed |
Virtual Adversarial Training on Graph Convolutional Networks in Node Classification 📝PRCV
| Model | SVAT, DVAT | Algorithm | Virtual Adversarial Training |
| Defense Type | Adversarial Training | Target Task | Node Classification |
| Target Model | GCN | Baseline | GCN |
| Metric | Accuracy | Dataset | Cora, CiteSeer, Pubmed |
Comparing and Detecting Adversarial Attacks for Graph Deep Learning 📝[email protected]
| Model | Algorithm | KL Divergence | |
| Defense Type | Detection Based | Target Task | Node Classification |
| Target Model | GCN, GAT | Baseline | |
| Metric | Classification Margin, Accuracy, ROC, AUC | Dataset | Cora, CiteSeer, PolBlogs |
Characterizing Malicious Edges targeting on Graph Neural Networks 📝ICLR OpenReview Code
| Model | SL, OD, GGD, LP+GGD, ENS | Algorithm | Link Prediction, Subsampling, Neighbour Analysis |
| Defense Type | Hybrid | Target Task | Node Classification |
| Target Model | GNN, GCN | Baseline | LP |
| Metric | AUC | Dataset | Cora, CiteSeer |
Latent Adversarial Training of Graph Convolution Networks 📝[email protected]
Batch Virtual Adversarial Training for Graph Convolutional Networks 📝ICML Code
| Model | S-BVAT, O-BVAT | Algorithm | atch Virtual Adversarial Training |
| Defense Type | Adversarial Training | Target Task | Node Classification |
| Target Model | GCN | Baseline | LP, DeepWalk, GAT, GPNN, GCN, VAT, ... |
| Metric | Accuracy | Dataset | Cora, CiteSeer, Pubmed, Nell |
αCyber: Enhancing Robustness of Android Malware Detection System against Adversarial Attacks on Heterogeneous Graph based Model 📝CIKM
| Model | Rad-HGC | Algorithm | HG-Defense |
| Defense Type | Detection Based | Target Task | Malware Detection |
| Target Model | Malware Detection System | Baseline | FakeBank, CryptoMiner, AppCracked, MalFlayer, GameTrojan, BlackBaby, ... |
| Metric | Detection Rate | Dataset | Tencent Security Lab Dataset |
Adversarial Robustness of Similarity-Based Link Prediction 📝ICDM
| Model | IDOpt, IDRank | Algorithm | Integer Program, Edge Ranking |
| Defense Type | Target Task | Link Prediction | |
| Target Model | Similarity-based Link Prediction Models | Baseline | PPN |
| Metric | DPR | Dataset | PA, PLD, TVShow, Gov |
mproving Robustness to Attacks Against Vertex Classification 📝[email protected]
| Model | SVM with a radial basis function kernel | Algorithm | Augmented Feature, Edge Selecting |
| Defense Type | Hybrid | Target Task | Node Classification |
| Target Model | SVM | Baseline | GCN |
| Metric | Classification Marigin | Dataset | Cora, CiteSeer |
Graph Adversarial Training: Dynamically Regularizing Based on Graph Structure 📝TKDE Code
| Model | GCN-GATV | Algorithm | raph Adversarial Training, Virtual Adversarial Training |
| Defense Type | Adversarial Training | Target Task | Node Classification |
| Target Model | GCN | Baseline | LP, DeepWalk, SemiEmb, Planetoid, GCN, GraphSGAN |
| Metric | Accuracy | Dataset | Cora, CiteSeer, NELL |
Adversarial Training Methods for Network Embedding 📝WWW Code
| Model | AdvT4NE | Algorithm | Adversarial Training |
| Defense Type | Adversarial Training | Target Task | Network embedding |
| Target Model | Deepwalk | Baseline | GF,DeepWalk, LINE,Node2vec, ... |
| Metric | Accuracy | Dataset | Cora, CiteSeer, Wiki, CA-GrQc, CA-HepTh |
GraphDefense: Towards Robust Graph Convolutional Networks 📝Arxiv
| Model | GraphDefense | Algorithm | Adversarial Training |
| Defense Type | Adversarial Training | Target Task | Node Classification |
| Target Model | GCN | Baseline | Drop Edges, Discrete Adversarial Training |
| Metric | Accuracy | Dataset | Cora, CiteSeer, Reddit |
Can Adversarial Network Attack be Defended? 📝Arxiv
| Model | Global-AT, Target-AT, SD, SCEL | Algorithm | Adversarial Training, Smooth Defense |
| Defense Type | Hybrid | Target Task | Node Classification |
| Target Model | GNN | Baseline | AT |
| Metric | ADR, ACD | Dataset | Cora, CiteSeer, PolBlogs |
Edge Dithering for Robust Adaptive Graph Convolutional Networks 📝Arxiv
| Model | AGCN | Algorithm | Adaptive GCN with Edge Dithering |
| Defense Type | Structure Based | Target Task | Node Classification |
| Target Model | GCN | Baseline | GCN |
| Metric | Accuracy | Dataset | Cora, CiteSeer, Pubmed, PolBlogs |
GraphSAC: Detecting anomalies in large-scale graphs 📝Arxiv
| Model | GraphSVC | Algorithm | Random, Consensus |
| Defense Type | Detection Based | Target Task | Anomaly Detection |
| Target Model | Anomaly Model | Baseline | GAE, Amen, Radar, Degree, ... |
| Metric | AUC | Dataset | Cora, CiteSeer, Pubmed, PolBlogs |
Adversarial Defense Framework for Graph Neural Network 📝Arxiv
| Model | DefNet | Algorithm | GAN, GER, ACL |
| Defense Type | Hybrid | Target Task | Node Classification |
| Target Model | GCN, GraphSAGE | Baseline | GCN, GraphSAGE |
| Metric | Classification Margin | Dataset | Cora, CiteSeer, PolBlogs |
Graph Interpolating Activation Improves Both Natural and Robust Accuracies in Data-Efficient Deep Learning 📝Arxiv Code
Adversarial Embedding: A robust and elusive Steganography and Watermarking technique 📝Arxiv
Examining Adversarial Learning against Graph-based IoT Malware Detection Systems 📝Arxiv
Target Defense Against Link-Prediction-Based Attacks via Evolutionary Perturbations 📝Arxiv
2018
Adversarial Personalized Ranking for Recommendation 📝SIGIR Code
| Model | APR, AMF | Algorithm | Adversarial Training based on MF-BPR |
| Defense Type | Adversarial Training | Target Task | Recommendation |
| Target Model | MF-BPR | Baseline | ItemPop, MF-BPR, CDAE, NeuMF, IRGAN |
| Metric | HR, NDCG | Dataset | Yelp, Pinterest, Gowalla |
2017
🔐 Robustness Certification
Collective Robustness Certificates 📝ICLR21
Adversarial Immunization for Improving Certifiable Robustness on Graphs 📝WSDM'21
Improving the Robustness of Wasserstein Embedding by Adversarial PAC-Bayesian Learning 📝AAAI'20
| Model | RAWEN | Algorithm | Adversarial PAC-Bayesian learning |
| Defense Type | Objective Based | Target Task | Node Embedding |
| Target Model | Wasserstein embedding | Baseline | GF, LINE, Node2vec, SDNE ... |
| Metric | Presion, Recall, AUC, F1 | Dataset | Wiki-Vote, Epinions, Google, Email,Wiki |
Certifying Robustness of Graph Laplacian Based Semi-Supervised Learning 📝ICLR'21 OpenReview
Certified Robustness of Graph Convolution Networks for Graph Classification under Topological Attacks 📝NeurIPS'20 Code
Certified Robustness of Community Detection against Adversarial Structural Perturbation via Randomized Smoothing 📝WWW'20
Efficient Robustness Certificates for Discrete Data: Sparsity - Aware Randomized Smoothing for Graphs, Images and More 📝ICML'20 Code
Abstract Interpretation based Robustness Certification for Graph Convolutional Networks 📝ECAI'20
Certified Robustness of Graph Classification against Topology Attack with Randomized Smoothing 📝NeurIPS'20
Certified Robustness of Graph Neural Networks against Adversarial Structural Perturbation 📝Arxiv'20
Certifiable Robustness to Graph Perturbations 📝NeurIPS'19 Code
⚖ Stability
Graph and Graphon Neural Network Stability 📝Arxiv'20
On the Stability of Graph Convolutional Neural Networks under Edge Rewiring 📝Arxiv'20
Stability of Graph Neural Networks to Relative Perturbations 📝ICASSP'20
Graph Neural Networks: Architectures, Stability and Transferability 📝Arxiv'20
Stability Properties of Graph Neural Networks 📝Arxiv'19
When Do GNNs Work: Understanding and Improving Neighborhood Aggregation 📝IJCAI'19 Workshop Code
Should Graph Convolution Trust Neighbors? A Simple Causal Inference Method 📝Arxiv'20
🚀 Others
Dynamic Knowledge Graph-based Dialogue Generation with Improved Adversarial Meta-Learning 📝Arxiv'20
Watermarking Graph Neural Networks by Random Graphs 📝Arxiv'20
📃 Survey
Deep Graph Structure Learning for Robust Representations: A Survey 📝IJCAI'21 Survey track
Graph Neural Networks Taxonomy, Advances and Trends 📝Arxiv'20
A Survey of Adversarial Learning on Graph 📝Arxiv'20
Adversarial Attacks and Defenses on Graphs: A Review and Empirical Study 📝Arxiv'20
Adversarial Attacks and Defenses in Images, Graphs and Text: A Review 📝Arxiv'19
Adversarial Attack and Defense on Graph Data: A Survey 📝Arxiv'18
Deep Learning on Graphs A Survey 📝Arxiv'18
🔗 Resource
- Awesome Adversarial Learning on Recommender System Link
- Awesome Graph Attack and Defense Papers Link
- Graph Adversarial Learning Literature Link
- A Complete List of All (arXiv) Adversarial Example Papers 🌐Link
- Adversarial Attacks and Defenses Frontiers, Advances and Practice, KDD'20 tutorial, 🌐Link
⚙ Toolbox
Note that the project description data, including the texts, logos, images, and/or trademarks,
for each open source project belongs to its rightful owner.
If you wish to add or remove any projects, please contact us at [email protected].