olafhartong / Threathunting
Programming Languages
Projects that are alternatives of or similar to Threathunting
ThreatHunting | A Splunk app mapped to MITRE ATT&CK to guide your threat hunts
This is a Splunk application containing several dashboards and over 130 reports that will facilitate initial hunting indicators to investigate.
You obviously need to be ingesting Sysmon data into Splunk, a good configuration can be found here
Note: This application is not a magic bullet, it will require tuning and real investigative work to be truly effective in your environment. Try to become best friends with your system administrators. They will be able to explain a lot of the initially discovered indicators.
Big credit goes out to MITRE for creating the ATT&CK framework!
Pull requests / issue tickets and new additions will be greatly appreciated!
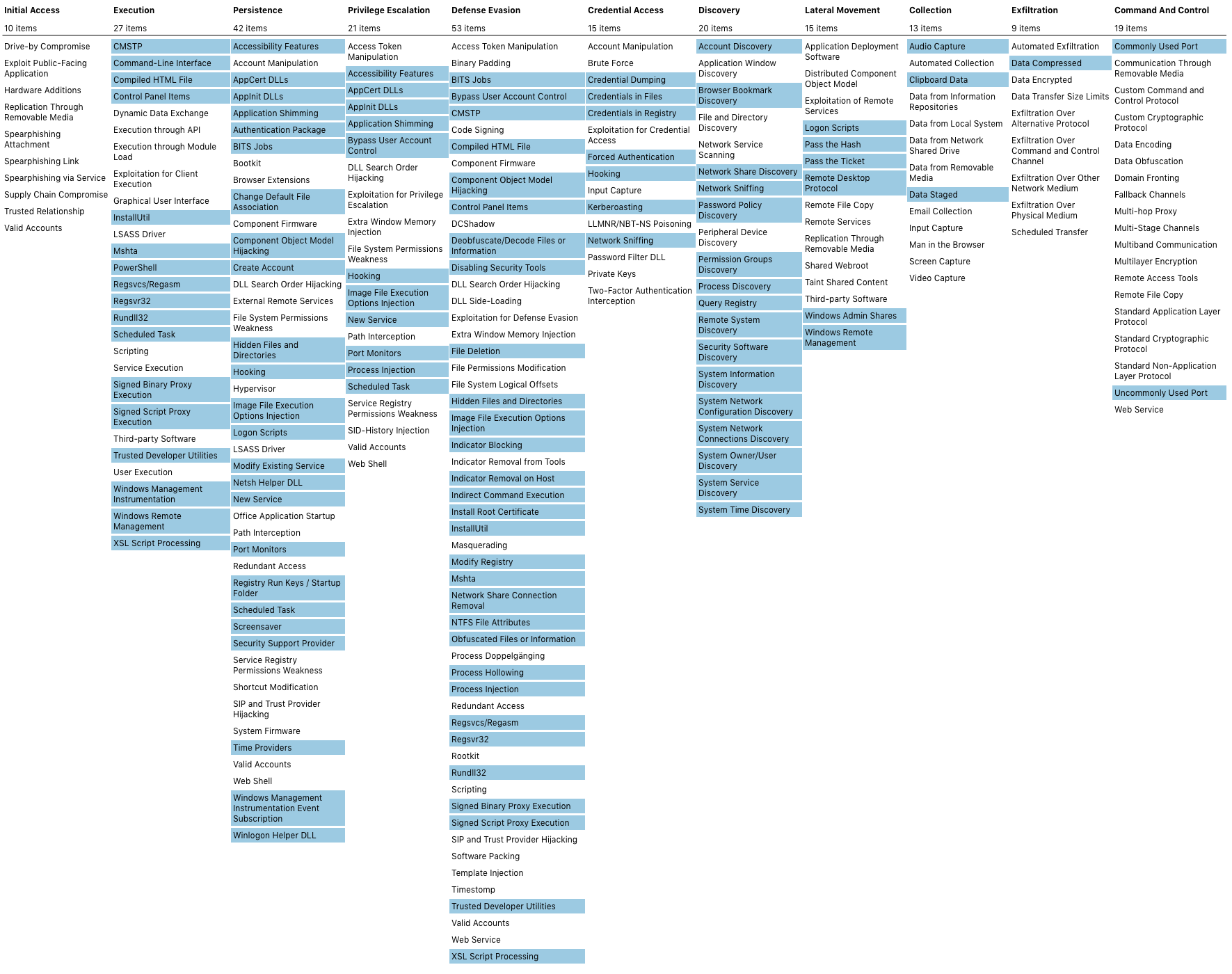
Mitre ATT&CK
I strive to map all searches to the ATT&CK framework.
A current ATT&CK navigator export of all linked configurations is found here and can be viewed here
App Prerequisites
Install the following apps to your SearchHead:
- Add-on for Microsoft Sysmon
- Punchcard Visualization
- Force Directed Visualization
- Sankey Diagram Visualization
- Lookup File Editor
Required actions after deployment
- Make sure the threathunting index is present on your indexers
- Edit the macro's to suit your environment > https://YOURSPLUNK/en-US/manager/ThreatHunting/admin/macros (make sure the sourcetype is correct)
- The app is shipped without whitelist lookup files, you'll need to create them yourself. This is so you won't accidentally overwrite them on an upgrade of the app.
- Install the lookup csv's or create them yourself, empty csv's are here
A step by step guide kindly written by Kirtar Oza can be found here
Usage
A more detailed explanation of all functions can be found here or in this blog post